By: Brij B. Gupta, Department of Computer Science and Information Engineering, Asia University, Taichung 413, Taiwan.
Abstract
As the edge devices grow more common, the tiny machine learning (TinyML) models are running at the network edge for low latency real-time inference and low energy consumption. While it enhances responsiveness and helps protect privacy, such a shift also increases the attack surface. Attacks targeting the distribution learning and inference pipelines, as well as compromised devices and insecure data exchange, can undermine trust in edge intelligence. Tiny edge models are currently faced with an array of security challenges. In this paper, we present a unified framework of defense-in-depth combining hardware isolation and cryptography with federated and distributed learning and blockchain-enabled integrity, all suitable to resource-limited settings.
Introduction
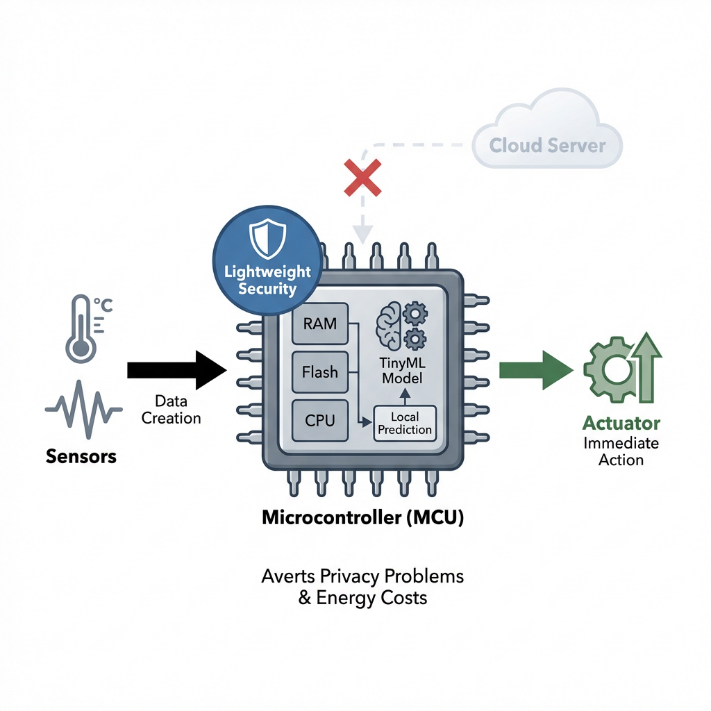
Edge AI brings intelligent decision-making closer to where data is created, be it sensors, actuators, or the user. Thanks to TinyML, predictions can be made on hardware types with limited resources like microcontrollers. This circumvents the process of sending information to remote servers. In doing so, privacy problems are averted, as well as the energy costs associated with communication. Nonetheless, the very limitations that make TinyML possible limited RAM, flash and processing power also constrain security controls. As a result, lightweight and effective protections are essential for trustworthy edge deployments [3]. In a multi-device or multi-user edge scenario, security is not only challenging but could also be complex due to data heterogeneity and decentralized governance. It gives rise to new safeguards like secure federated learning and immutable provenance [4], [5]. Given this background, the article provides a survey of layered security (hardware isolation, cryptographic agility, security of distributed learning, blockchain enabled integrity) that empowers tiny models to deliver high impact results without incurring prohibitive cost to energy or latency [3], [6].
Threat Landscape for Edge Tiny Models
Data Privacy and Confidentiality in Edge Environments
It is better to keep data close to the source in edge deployments to reduce the risks of a breach on a central store. Nevertheless, sensitive data will still leak through analytics output, traffic metadata, and poorly secured updates. Secure aggregation in federated learning and encrypted on-device computation are lightweight, edge-enabled privacy mechanisms that can limit leakages while keeping things responsive [7], [8]. The Internet of Medical Things (IoMT) establishes stringent regulations and clinical specifications. Therefore, protecting on-device inference with privacy-preserving primitives is crucial. (21 words)
Model Integrity and Poisoning Attacks
Decentralized learning at edge includes model updates and federation across heterogeneous devices subject the models to data poisoning and backdoor or trojan threats. A security-aware aggregation approach that utilizes defence strategies helps in testing, validating, and self-reorganizing system of AIoT. This restricts the poisoning of samples and reduces the chances of updates getting disrupted. The amalgamation of federated learning with edge constraints needs the explicit security guarantees of update integrity and adversarial manipulation [4].
Authentication and Access Control
Need help with authentication and authorization? Place an order now. The post Authentication and authorization for edge platforms appeared first on The Writersbid. Authentication schemes that lightweight and designed for edge devices must balance between security strength and energy, latency, and computational overhead while ensuring user privacy [7]. To reduce attacks’ windows and exposure in outdoor or dynamic edge deployments, time-bound or context-aware authentication approaches can be used.
Resource Constraints and Attack Surface
Tiny edge devices offer limited protection budgets, so conventional security protocols must be reimagined to fit tight energy and memory budgets. The need for hardware-assisted isolation and efficient secure computation is pronounced in TinyML contexts, where even modest added latency or power use can undermine a system’s real-time guarantees [3].
Data Provenance and Integrity in Edge Pipelines
Edge pipelines often combine sensing, local inference, and occasional cloud or fog coordination. Ensuring data provenance, tamper-evidence, and auditable execution paths is essential to sustain trust in edge analytics, particularly when decisions affect safety-critical operations or public resources [5].
Core Security Mechanisms for Tiny Edge AI
Hardware- and OS-level Isolation: Trust and Hardware Trust Mechanisms
Hardware-supported protection, like secure enclaves and trusted execution environments, offers an essential defense against tampering with edge inference pipelines and model parameters. Creatively utilizing – only for the most sensitive data or model layers– a small amount of trusted execution resources can yield good performance trade-offs for TinyML on constrained devices [3].
Cryptographic Foundations and Post-Quantum Readiness
Increasingly seen as a necessity for edge security of long-lived deployments, post-quantum cryptography is expected to become a requirement in IoMT and AIoT ecosystems due to their extended data security needs. Lightweight PQC methods deployed at the edge can enable us to provide confidentiality and integrity properties necessary for long-term resilience for edge-based analytics and cloud or fog layer communication [9], [4]. Edge architectures with PQC support secure key exchange and long-term confidentiality of data sent to distributed nodes and federated learning coordinators [9].
Federated Learning Security and Privacy
Federated learning (FL) suits the needs of TinyML by keeping data local and aggregating updated models/gradients. Yet, FL faces novel security and privacy challenges, such as poisoning attacks and communication-security threats. Recent literature proposes strong aggregation rules for secure aggregation and introduction of privacy-preserving training protocols, which will protect the participants from leakage of inference and adversarial update in AIoT scenarios [4], [10]. FL frameworks that operate with an edginess focus have become more popular as they maintain the utility of the model and privacy of users [10].
Blockchain, Distributed Ledger, and Secure Content Integrity at the Edge
Blockchain and distributed ledger technologies offer attractive characteristics for edge security, such as tamper-resistance and provenance. The Edge security architectures’ functionalities include using blockchain-enhanced content caching and secure offloading to prevent adversarial manipulations of edge resources and to generate auditable traces from critical decisions. In conjunction with FL, blockchain technology can facilitate integrity and non-repudiation in collaborative edge learning [6].
Authentication and Access Management for Lightweight Edge Ecosystems
Lightweight, adaptive authentication mechanisms are essential for edge deployments where devices frequently join or leave networks and operate in dynamic contexts. Time-bound and dynamic key generation techniques help limit risk exposure in outdoor edge nodes [7].
Architectures, Patterns, and Design Considerations
All-On-Edge versus Edge–Cloud Secure Collaboration
Designs that place all security enforcement at the edge must optimize for ultra-low power, memory, and compute budgets; alternatively, edge–cloud collaborations can offload heavier cryptographic or aggregation tasks while preserving privacy and latency guarantees. Recent surveys emphasize lightweight FL architectures and cloud–edge collaborations as viable paths to scalable, privacy-preserving AI at the edge, with practical guidance for secure orchestration [10].
Secure Offloading, Scheduling, and Resource-Aware Security
Secure offloading decisions—balancing latency, energy, and security risk—are central to edge systems that rely on heterogeneous devices and intermittent connectivity. AI-enhanced task execution frameworks can improve responsiveness while enabling security-conscious offloading decisions that respect device constraints and network conditions [10].
Lightweight Security Primitives for TinyML
To preserve the tight energy and latency budgets of TinyML, security primitives must be carefully engineered for constrained hardware. Hardware-assisted isolation and small-footprint cryptographic schemes are essential to maintain practical performance in edge AI deployments [3].
Data Provenance, Integrity, and Trust in Edge Pipelines
Combining secure data provenance with tamper-evident inferences is critical for trusted edge analytics, especially in healthcare and safety-critical domains. Blockchain-enabled provenance and authenticated data flows support auditable decision trails while dovetailing with FL and PQC strategies to preserve privacy and integrity across distributed edge nodes [5].
Case Studies and Applications
IoMT and ICU Monitoring with TinyML and PQC
A secure edge-based IoMT framework demonstrates how TinyML can operate at the edge for real-time monitoring while leveraging PQC to secure communications and long-term data protection in healthcare settings [9]. This approach aligns with broader edge strategies that preserve patient privacy while enabling responsive clinical insights [6].
Secure Edge-Enabled Diagnostics and Telemetry
Edge-based medical diagnostics and remote monitoring can benefit from a hybrid security stack that includes hardware isolation, secure aggregation for learning from distributed patient data, and blockchain-backed integrity for data provenance and model updates [6].
Lightweight Authentication in Outdoor Edge Deployments
IoT edge deployments used for outdoor sensing and public-safety applications rely on efficient authentication to prevent unauthorized access and data tampering. Time-bound key generation and selective TrustZone protection provide practical mechanisms for maintaining trust with minimal energy overhead in edge contexts [3].
Conclusion
Tiny edge models have a big impact by delivering intelligence in real-time at the edge of the network while protecting copyrights as well. It is essential that the security posture offers hardware-based isolation, quantum-resistant cryptography, secure distributed learning, and distributed ledger guarantees for confidentiality, integrity, and availability in constrained environments. Through the synergy of on-device inference accompanied by hardware-assisted protections, secure aggregation for federated learning, blockchain provenance, and adaptive authentication, one can achieve practical and scalable security solutions for IoMT, smart cities, and other edge-based AI ecosystems.
References
- A. Velichko, “A Method for Medical Data Analysis Using the LogNNet for Clinical Decision Support Systems and Edge Computing in Healthcare”, Sensors, vol. 21, no. 18, p. 6209, 2021. https://doi.org/10.3390/s21186209
- X. Liu, B. Li, S. Chen, & Z. Xu, “A Survey on Multi-User Privacy Issues in Edge Intelligence: State of the Art, Challenges, and Future Directions”, Electronics, vol. 14, no. 12, p. 2401, 2025. https://doi.org/10.3390/electronics14122401
- H. Yang, R. Dong, R. Guo, Y. Che, X. Xie, J. Yanget al., “Real-Time Acoustic Scene Recognition for Elderly Daily Routines Using Edge-Based Deep Learning”, Sensors, vol. 25, no. 6, p. 1746, 2025. https://doi.org/10.3390/s25061746
- J. Tu, L. Yang, & J. Cao, “Distributed Machine Learning in Edge Computing: Challenges, Solutions and Future Directions”, Acm Computing Surveys, vol. 57, no. 5, p. 1-37, 2025. https://doi.org/10.1145/3708495
- Y. Yoon, D. Hwang, J. Yang, & S. Lee, “Intellino: Processor for Embedded Artificial Intelligence”, Electronics, vol. 9, no. 7, p. 1169, 2020. https://doi.org/10.3390/electronics9071169
- K. Yang, Y. Shi, W. Yu, & Z. Ding, “Energy-Efficient Processing and Robust Wireless Cooperative Transmission for Edge Inference”, Ieee Internet of Things Journal, vol. 7, no. 10, p. 9456-9470, 2020. https://doi.org/10.1109/jiot.2020.2979523
- J. Aramendia, A. Cabrera, J. Martín, J. Gumiel, & K. Basterretxea, “Neural Network Implementation for Fire Detection in Critical Infrastructures: A Comparative Analysis on Embedded Edge Devices”, Electronics, vol. 14, no. 9, p. 1809, 2025. https://doi.org/10.3390/electronics14091809
- C. Han, T. Yang, X. Sun, & Z. Cui, “Secure Hierarchical Federated Learning for Large-Scale AI Models: Poisoning Attack Defense and Privacy Preservation in AIoT”, Electronics, vol. 14, no. 8, p. 1611, 2025. https://doi.org/10.3390/electronics14081611
- Y. Akbari, “Atrial Fibrillation Detection on the Embedded Edge: Energy-Efficient Inference on a Low-Power Microcontroller”, Sensors, vol. 25, no. 21, p. 6601, 2025. https://doi.org/10.3390/s25216601
- S. Zhan, L. Huang, G. Luo, S. Zheng, Z. Gao, & H. Chao, “A Review on Federated Learning Architectures for Privacy-Preserving AI: Lightweight and Secure Cloud–Edge–End Collaboration”, Electronics, vol. 14, no. 13, p. 2512, 2025. https://doi.org/10.3390/electronics14132512
Cite As
Gupta B.B. (2026) Edge AI Security: Protecting Tiny Models with Big Impact, Insights2Techinfo, pp.1