By: Akshat Gaurav, Ronin Institute, Montclair, NJ, USA
The integration of artificial intelligence (AI) and automation into Security Operations Centers (SOCs) is revolutionizing how organizations detect and respond to cybersecurity threats. SOC teams, which typically consist of a small group of analysts, are tasked with monitoring, detecting, and mitigating security incidents across diverse environments, including on-premises infrastructure and cloud platforms. As the volume and sophistication of cyber threats continue to escalate, the adoption of AI-driven tools and automated processes is becoming essential for enhancing threat detection capabilities and operational efficiency within SOCs.[1][2][3].
AI empowers SOC teams to transition from reactive alert management to proactive threat hunting by automating routine tasks and providing advanced analytical insights. Techniques such as machine learning and natural language processing enable analysts to identify hidden threats and anomalies that traditional security measures might overlook.[4][5][3]. This evolution is notable as it not only improves the efficacy of threat detection but also alleviates common challenges such as alert fatigue, where analysts are overwhelmed by the sheer volume of alerts.[6][7].
Additionally, the collaboration between human expertise and AI tools fosters a more strategic approach to cybersecurity, allowing analysts to focus on complex investigations rather than repetitive tasks.[3][8].
However, the integration of AI and automation within SOCs is not without its controversies and challenges. Issues such as the complexity of advanced threats, high false positive rates, and the shortage of qualified personnel hinder effective threat hunting and incident response.[9][10][11]. Organizations must also grapple with the resource implications of implementing AI solutions, including budget constraints and the need for continuous training to keep staff updated on evolving technologies.[12][13]. As cybersecurity threats become increasingly sophisticated, addressing these operational challenges while harnessing the power of AI will be critical for the future of SOC operations.[14][13].
SOC Teams
The Security Operations Center (SOC) plays a critical role in maintaining the cyber- security posture of organizations by monitoring, detecting, and responding to security threats. SOC teams are typically composed of a small number of full-time analysts, often ranging from 2 to 10 members, which has remained consistent in recent years despite the expanding scope of security responsibilities across various platforms, including on-premises infrastructure, cloud environments, and remote endpoints[1]. This lean structure, while cost-effective, can lead to systemic burnout among team members, presenting a significant challenge that organizations must address to ensure effective threat management[1].
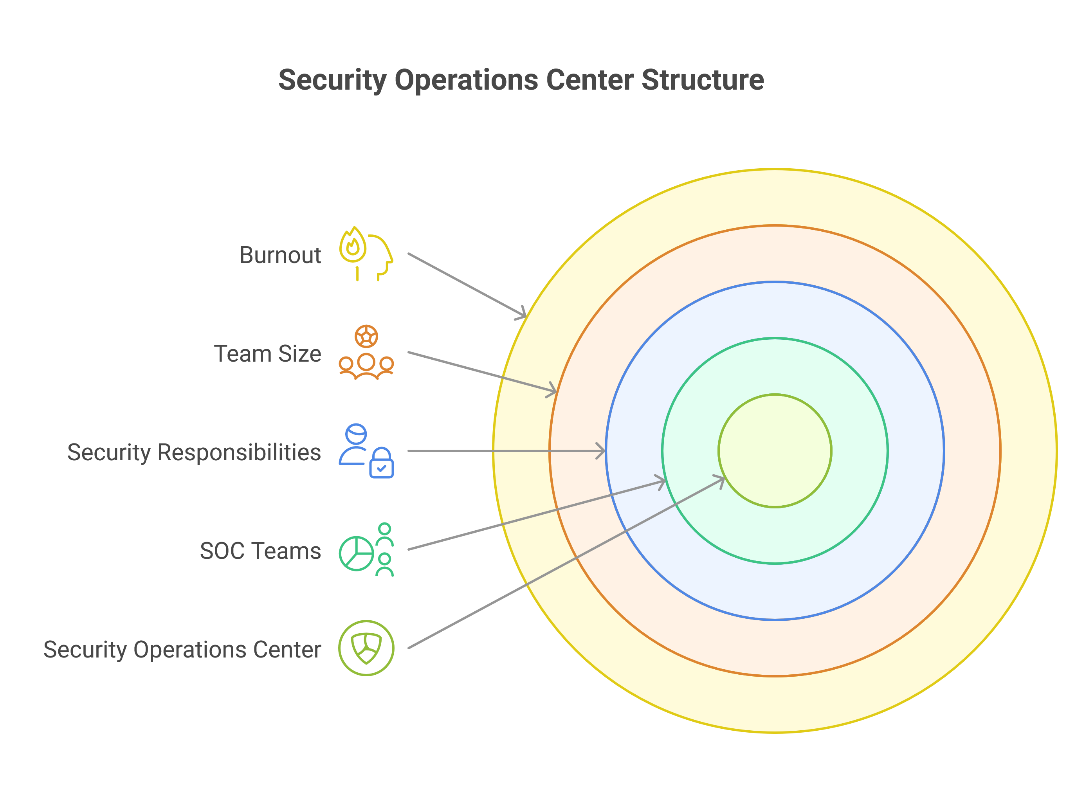
Roles and Responsibilities
Establishing well-defined roles within SOC teams is essential for operational efficiency. Team members should have clear responsibilities that align with their expertise, such as tier-one analysts who manage initial alerts, advanced threat hunters who investigate complex threats, and incident responders who mitigate attacks[15]. This structured approach helps minimize redundancy and ensures that security incidents are escalated efficiently to the appropriate personnel. Additionally, modern SOCs are integrating artificial intelligence (AI) into their workflows, allowing analysts to adopt hybrid roles that emphasize strategic thinking and decision-making rather than routine monitoring[15][16].
Training and Development
Investing in training and development programs is vital for SOC teams to stay updated on the latest security threats and trends[17]. Ongoing education not only helps in retaining staff, reducing turnover rates, but also enhances the overall effectiveness of the SOC. Various training models, including hands-on simulations, are recommended to maintain engagement and facilitate better knowledge retention. Certifications such as the CISA (Certified Information Systems Auditor) provide team members with additional credentials that bolster their capabilities in monitoring and auditing an organization’s IT assets[17].
Metrics and Performance
SOC metrics are crucial for assessing the performance and effectiveness of security operations. Commonly used metrics include Mean Time to Detect (MTTD), which measures the average time taken to identify a security incident[18]. By tracking these metrics, SOC teams can gauge their effectiveness in detecting and responding to threats, helping to inform future operational strategies. Continuous improvement is essential, as organizations strive to remain competitive and secure in an everevolving threat landscape[18].
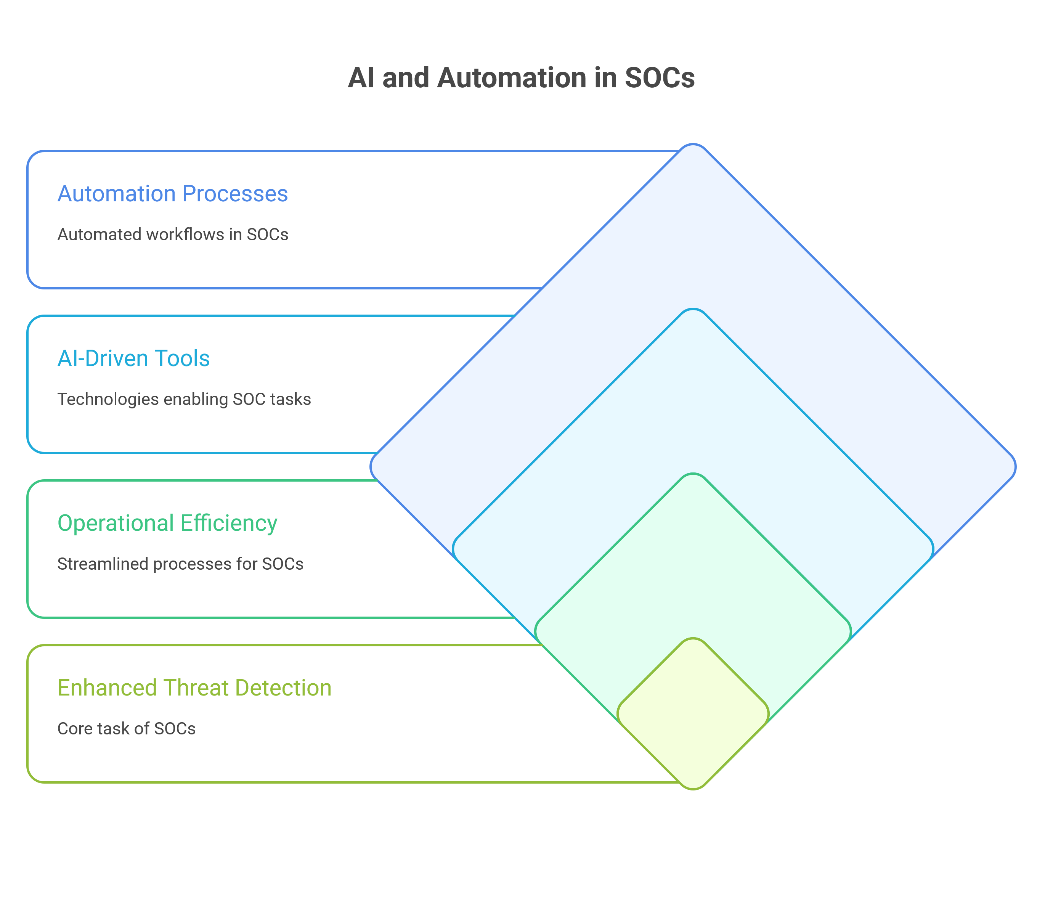
Integration of AI and Automation
The integration of AI and automation into Security Operations Centers (SOCs) is transforming the way organizations manage and respond to cyber threats. While automation typically refers to predefined tasks being executed without human intervention, AI introduces dynamic capabilities that enable systems to adapt to new information and investigation contexts[19]. This distinction is crucial as AI not only complements automation but also enhances its effectiveness in threat detection and response.
Enhancing Security Operations
AI technologies empower SOC teams by providing advanced threat detection capabilities, predictive analytics, and real-time monitoring. For instance, AI systems analyze large volumes of data to identify behavioral patterns, enabling the detection of anomalies that could indicate a security breach[3]. By continuously learning and adapting, these AI models improve over time, ensuring that they remain effective against evolving cyber threats[20]. This proactive approach shifts SOC operations from a reactive stance to a more anticipatory mode, allowing teams to hunt for threats before they materialize into incidents[21].
Collaborative Dynamics
Contrary to the belief that AI and automation may replace human analysts, the integration of these technologies aims to complement human expertise. AI enhances the decision-making process by summarizing vast amounts of data and prioritizing alerts, thereby reducing alert fatigue among analysts[3]. By taking on routine and repetitive tasks, AI enables security professionals to focus on more complex issues, fostering a collaborative environment where human intuition and AI efficiency work hand in hand[3][8]. This collaboration is essential for building analyst confidence, as it allows for more targeted feedback and coaching based on performance metrics[1].
Seamless Integration with Existing Systems
For organizations looking to adopt AI in their SOCs, smooth integration with existing security infrastructure is imperative. AI solutions often come equipped with APIs or connectors that facilitate this integration, allowing them to enhance traditional security tools such as firewalls and intrusion detection systems[8]. This compatibility ensures that AI does not replace existing systems but rather augments their capabil- ities, leading to a more robust and responsive security posture.
Implementation Challenges
Despite the advantages, the transition to an AI-powered SOC is not without challenges. Organizations like DXC Technology have demonstrated the necessity of a structured implementation roadmap, beginning with low-risk automation and progressively integrating advanced features like anomaly detection[20][18]. As the complexity of cyber threats increases, the ability to scale and adapt security operations becomes paramount. The integration of AI and automation not only addresses scalability issues but also helps mitigate alert fatigue, enabling SOC teams to respond more effectively to emerging threats[22].
AI in Threat Hunting
AI is fundamentally transforming the landscape of threat hunting within cybersecurity operations. By integrating artificial intelligence, security operations center (SOC) teams can proactively identify hidden threats that traditional security measures often miss. This section explores the role of AI in modern threat hunting, highlighting its benefits, methodologies, and future potential.
Benefits of AI in Threat Hunting
The implementation of AI in threat hunting offers several advantages:
Automation of Routine Tasks: AI can automate time-consuming activities, such as log analysis and data correlation, allowing human analysts to focus on more strategic aspects of threat hunting[4][6]. Behavioral Analysis: Unlike traditional security tools that rely on signature-based detection, AI can analyze user, device, and application behavior over time. This capability allows for the identification of deviations from normal behavior, which may signal malicious activities[4]. Advanced Anomaly Detection: AI tools can identify unusual network behaviors that might suggest a cyberattack, detecting malware and ransomware before they inflict damage[23].
Examples of AI-Driven Behavioral Threat Hunting
User Behavior Analytics (UBA): AI tracks typical user interactions with systems and flags unusual activities, such as unexpected logins or access to sensitive data outside of normal patterns[4].
Network Traffic Analysis: AI continuously monitors network traffic for anomalies that could indicate data exfiltration or command-and-control operations by cybercriminals[4].
The Role of AI in Modern Threat Hunting
AI technologies, particularly machine learning (ML) and deep learning, empower SOC teams to process vast amounts of security data efficiently. These systems are capable of recognizing complex patterns and behaviors that may indicate potential threats, thus enabling a shift from reactive to proactive threat hunting strategies[4][6]. AI’s ability to adapt and improve over time further enhances its effectiveness in identifying emerging attack techniques[4].
Natural Language Processing (NLP) in Threat Hunting
Natural Language Processing (NLP) enhances threat hunting by enabling AI systems to sift through large volumes of unstructured data, such as threat reports and dark web discussions, to extract actionable intelligence. This intelligence helps analysts focus on the most pertinent threats, ensuring a more efficient response to potential incidents[4][5].
Key Use Cases for NLP in Threat Hunting
Automated Threat Intelligence: AI can scan through extensive online resources, highlighting new vulnerabilities or attack techniques that warrant investigation[4]. Contextual Threat Analysis: By understanding the context of threats—such as their potential impact on specific sectors—NLP allows for more informed decision-making by SOC teams[4].
The Future of AI in Threat Hunting
As cyber threats continue to evolve, the integration of AI within threat hunting strategies will only increase. Future developments may include AI-driven deception tactics to lure attackers into revealing their methods, thereby enhancing threat detection capabilities[4]. Additionally, advancements in technologies such as quantum-resistant algorithms and autonomous security operations centers (SOCs) promise to further bolster the role of AI in cybersecurity[4].
Automation in Threat Hunting
Automation plays a crucial role in enhancing the efficiency and effectiveness of threat hunting within Security Operations Centers (SOCs). As cyber threats continue to evolve in complexity and volume, the integration of advanced technologies, particu- larly Artificial Intelligence (AI) and Machine Learning (ML), has become essential for organizations to maintain robust security postures.
Key Benefits of Automation
Improved Threat Detection and Response
Automated threat hunting platforms leverage machine learning algorithms to contin- uously scan for suspicious activity across networks and systems. These platforms can enrich alerts with contextual information, enabling faster investigations and more effective threat identification[24][25]. Automation allows SOC teams to aggregate and analyze extensive datasets from diverse sources, facilitating the detection of anomalies and patterns that may indicate concealed threats[24][26]. This proactive approach enhances overall threat detection capabilities, as automated systems can identify overlooked anomalies that may signify emerging security incidents[3].
Reduction of Alert Fatigue
The overwhelming volume of security alerts—averaging thousands per day—has led to significant alert fatigue among SOC analysts[6]. AI-driven alert triage systems have become indispensable for addressing this issue, as they analyze alert metadata and historical patterns to filter out false positives and prioritize genuine threats for further analysis[6][7]. By automating the alert triage process, organizations can reduce the cognitive load on analysts, allowing them to focus on more critical investigations rather than being overwhelmed by noise.
Increased Scalability and Resource Optimization
Automation not only improves the speed and accuracy of threat detection but also enhances the scalability of security operations[3]. As threats multiply, automated systems enable SOCs to handle larger workloads without necessitating proportional increases in human resources[26]. By minimizing manual effort, automation opti- mizes resource utilization and lowers operational costs, ultimately providing a higher return on investment for cybersecurity operations[26].
Implementation Strategies
Developing Customized Detection Libraries
To maximize the effectiveness of automation in threat hunting, SOC teams should develop customized detection rules and signatures tailored to their specific threat landscape[3]. This library of detection capabilities should be continuously updated based on the latest threat intelligence and incident data to ensure that automated systems remain effective against new and evolving threats.
Monitoring and Continuous Improvement
Regular evaluation of automated security operations is essential to identify gaps and areas for improvement. SOC teams should document and measure key performance metrics, such as response time reductions and error rates, to continuously optimize their automated processes[3]. This ongoing improvement ensures that automation remains aligned with organizational goals and adapts to the changing cybersecurity landscape.
Integration of AI and Automation
The integration of AI and automation into Security Operations Centers (SOCs) is transforming the way organizations manage and respond to cyber threats. While automation typically refers to predefined tasks being executed without human intervention, AI introduces dynamic capabilities that enable systems to adapt to new information and investigation contexts[19]. This distinction is crucial as AI not only complements automation but also enhances its effectiveness in threat detection and response.
Enhancing Security Operations
AI technologies empower SOC teams by providing advanced threat detection capabilities, predictive analytics, and real-time monitoring. For instance, AI systems analyze large volumes of data to identify behavioral patterns, enabling the detection of anomalies that could indicate a security breach[3]. By continuously learning and adapting, these AI models improve over time, ensuring that they remain effective against evolving cyber threats[20]. This proactive approach shifts SOC operations from a reactive stance to a more anticipatory mode, allowing teams to hunt for threats before they materialize into incidents[21].
Collaborative Dynamics
Contrary to the belief that AI and automation may replace human analysts, the integration of these technologies aims to complement human expertise. AI enhances the decision-making process by summarizing vast amounts of data and prioritizing alerts, thereby reducing alert fatigue among analysts[3]. By taking on routine and repetitive tasks, AI enables security professionals to focus on more complex issues, fostering a collaborative environment where human intuition and AI efficiency work hand in hand[3][8]. This collaboration is essential for building analyst confidence, as it allows for more targeted feedback and coaching based on performance metrics[1].
Seamless Integration with Existing Systems
For organizations looking to adopt AI in their SOCs, smooth integration with existing security infrastructure is imperative. AI solutions often come equipped with APIs or connectors that facilitate this integration, allowing them to enhance traditional security tools such as firewalls and intrusion detection systems[8]. This compatibility ensures that AI does not replace existing systems but rather augments their capabilities, leading to a more robust and responsive security posture.
Implementation Challenges
Despite the advantages, the transition to an AI-powered SOC is not without challenges. Organizations like DXC Technology have demonstrated the necessity of a structured implementation roadmap, beginning with low-risk automation and progressively integrating advanced features like anomaly detection[20][18]. As the complexity of cyber threats increases, the ability to scale and adapt security operations becomes paramount. The integration of AI and automation not only addresses scalability issues but also helps mitigate alert fatigue, enabling SOC teams to respond more effectively to emerging threats[22].
Challenges and Limitations
Despite the increasing integration of AI and automation in Security Operations Centers (SOCs), several challenges and limitations persist that hinder their effectiveness in threat hunting.
Complexity of Advanced Threats
Emerging threats often do not conform to known patterns or predefined rules, which complicates detection with traditional security tools[9]. The dynamic nature of cyber threats necessitates advanced analytical capabilities that many SOCs struggle to implement, leading to vulnerabilities in security postures.
Human Resource Limitations
A significant challenge facing SOCs is the lack of qualified personnel, particularly experienced threat hunting analysts[9]. This shortage limits the depth and effectiveness of investigations, as teams are often overwhelmed by a high volume of daily alerts. Consequently, the workload management becomes critical; SOC teams frequently find themselves prioritizing incident response over proactive threat hunting[9][27].
Lack of Time and Prioritization
Most SOCs allocate the majority of their time to incident response and alert management, leaving insufficient resources for threat hunting activities. Studies indicate that only a small percentage of critical alerts are investigated thoroughly[9]. This lack of prioritization can lead to overlooked threats and compromised security.
Tools and Data Complexity
The integration and correlation of data from various sources, such as endpoints, network traffic, and cloud systems, require sophisticated tools and specific skill sets[9]. However, managing the complexity of these tools and the data they generate can be time-consuming and burdensome for SOC teams, which further exacerbates the challenge of effective threat hunting.
False Positive Rates
False positive rates (FPR) are a crucial performance metric for SOCs as they measure the quality of detection systems. A high FPR indicates that SOC analysts waste time on non-threatening alerts, which can obscure real threats and weaken overall defenses[10][28]. Reducing the false positive rate requires constant tuning of detection rules and a careful balance between true and false positives, a task that demands significant resources and expertise[29][30].
Resource Constraints
Implementing AI-driven solutions in SOCs can be hindered by resource constraints, including budget limitations and the high cost of legacy systems[11]. Evaluating new tools requires a clear understanding of their implementation requirements and potential disruptions to existing workflows. Without a cost-effective solution, many SOCs may struggle to keep pace with evolving threats and maintain compliance with regulatory standards[23][12].
Future Trends
The future of Security Operations Centers (SOCs) is poised for transformation, primarily driven by advancements in artificial intelligence (AI), automation, and the growing complexity of cybersecurity challenges. As organizations increasingly rely on digital ecosystems, the tools utilized by SOCs will need to evolve significantly to enhance threat detection, response capabilities, and overall operational efficiency.
Advancements in AI and Automation
The SOC of tomorrow will feature highly automated systems capable of not only detecting threats but also mitigating and potentially predicting them before they occur. AI and machine learning models will evolve to analyze data patterns continuously, allowing for minimal human intervention in threat identification and resolution processes[31][32]. This shift will enable organizations to respond to incidents in real-time, automating many routine tasks that currently consume significant analyst time.
Moreover, predictive analytics will play a crucial role in forecasting future threats. By leveraging historical data and current trends, SOCs will be able to strengthen their defenses proactively[32]. Continuous refinement of predictive models will enhance accuracy over time, enabling security teams to focus resources on high-probability threats and implement preemptive measures accordingly[33].
The Evolving Role of SOC Analysts
As automation takes over repetitive tasks, the role of SOC analysts will shift from reactive responders to strategic leaders in cybersecurity[34]. Analysts will become “supercharged” professionals, equipped with advanced decision-support tools that empower them to make informed, nuanced judgments under uncertainty. This trans- formation will not only enhance the operational impact of analysts but also help mitigate burnout by alleviating their workloads[14]. Organizations will need to invest in training and development to ensure that their teams are adept at leveraging these new technologies effectively[13].
Building an AI-Native SOC
To fully realize the potential of an AI-native SOC, organizations must carefully select technologies that complement their existing infrastructure[13]. This includes assem- bling multidisciplinary teams with expertise in AI, cybersecurity, and data science to manage the implementation of AI solutions. Ongoing training will be vital to keep these teams at the forefront of technological advancements and to develop innovative security protocols[35][36].
Addressing Operational Challenges
Despite the promise of AI and automation, organizations must navigate several operational challenges to maintain effective security operations. These include the increasing sophistication of cyber threats and the complexity of digital infrastructures, which can overwhelm existing security teams[14]. Addressing these challenges will be critical not only for robust security postures but also for the professional development and mental health of SOC analysts.
References
- : How AI-Enabled Workflow Automation Can Help SOCs Reduce …
- : SOC Best Practices for Tackling Modern Threats [2025]
- : How Executives Can Improve Team Efficiency And Collaboration …
- : How Do I Improve SOC Effectiveness? – Palo Alto Networks
- : SOC Metrics: Security Metrics & KPIs for Measuring SOC Success
- : 7 Cybersecurity Monitoring Tools Every SOC Analyst Should Master
- : Threat Hunting with AI — How Autonomous Systems Are Changing …
- : Real-World Use Cases of AI-Powered SOC [2025] – Radiant Security
- : What Are the Barriers to AI Adoption in Cybersecurity? – Palo Alto …
- : What Is the Role of AI in Security Automation? – Palo Alto Networks
- : An Introduction to SOC Automation – Torq
- : Threat Hunting in SOC: Techniques and Tools – Cado Security
- : Work Smarter in 2025: 7 Benefits of Automating CTI into SOC Activities
- : What is SOC Automation? Improving Security Workflows and …
- : Automated Security Operations Centers (SOC): How AI is Changing …
- : Incorporating AI agents into SOC workflows | Red Canary
- : The AI-Driven SOC (R)evolution | AI Case Studies
- : How SOC Teams Use Agentic AI & Co-Pilot AI to Reduce Risk
- : AI Threat Detection: Leverage AI to Detect Security Threats
- : Power of Machine Learning in Cybersecurity for Defending Digital …
- : The challenges of Threat Hunting for the SOC – CyberTrust 365
- : 10 Key SOC Challenges and How AI Addresses Them
- : 5 Key Metrics to Track for Effective Security Operations – Fortinet
- : SOC Metrics: The Key Metrics & KPIs to Measure Your SOC Success
- : Machine Learning (ML) in Cybersecurity: Use Cases – CrowdStrike
- : The Clock’s Ticking: How SOC KPIs Reveal Security Gaps
- : Evaluation Criteria AI SOC Analysts – Radiant Security
- : Top 15 SOC Automation Tools in 2025 – Zluri
- : The Future SOC – How AI, Automation, and Decentralization Will …
- : What is AI-Driven Threat Detection and Response? – Radiant Security
- : Machine Learning in Cybersecurity: A Primer for Beginners – Tanium
- : AI-Driven SOC: The Next Evolution in Security Operations
- : The Top Challenges Faced by SOC Analysts – Radiant Security
- : Building an AI-Native Security Operations Center – Cisco Blogs
- : The Long Road to Automating the SOC – Activant Capital
- : How AI Takes Collaboration Tools to the Next Level – Cerium Networks
- Kumar, A., Shankar, A., Behl, A., Gupta, B. B., & Mavuri, S. (2023). Lights, camera, metaverse!: eliciting intention to use industrial metaverse, organizational agility, and firm performance. Journal of Global Information Management (JGIM), 31(8), 1-20.
- Liu, R. W., Guo, Y., Lu, Y., Chui, K. T., & Gupta, B. B. (2022). Deep network-enabled haze visibility enhancement for visual IoT-driven intelligent transportation systems. IEEE Transactions on Industrial Informatics, 19(2), 1581-1591.
Cite As
Gaurav A. (2025) How SOC Teams Use AI and Automation to Hunt Threats, Insights2Techinfo, pp.1