By: Aiyaan Hasan, International Center for AI and Cyber Security Research and Innovations (CCRI), Asia University, Taiwan, rayhasan114@gmail.com
Abstract
We are surrounded with potential cyber threats and vulnerabilities in this interconnected modern world, developing strategies to protect virtual assets, user data and virtual environments has become absolutely crucial. It might also involve an analysis of emerging threats and how they are different from any other traditional cybersecurity challenges.
Introduction
The concept of the metaverse has evolved as a transformative force when it comes to the digital realm, it has redefined the wat we interact, work, play and connect to the online world. Metaverse is a virtual universe in the simplest of terms, a mixture of both physical and digital realms, where individuals have the ability to engage in immersive experiences, they can also interact with each other by utilizing their own customized avatars and explore limitlessly[8-12].
When it comes to metaverse, the boundary between reality and the digital world is ambiguous, users are able to access and navigate the ever-expanding digital landscapes and can interact with people across the globe, ranging from gaming and entertainment to education and what not – All within a shared and interconnected virtual world.
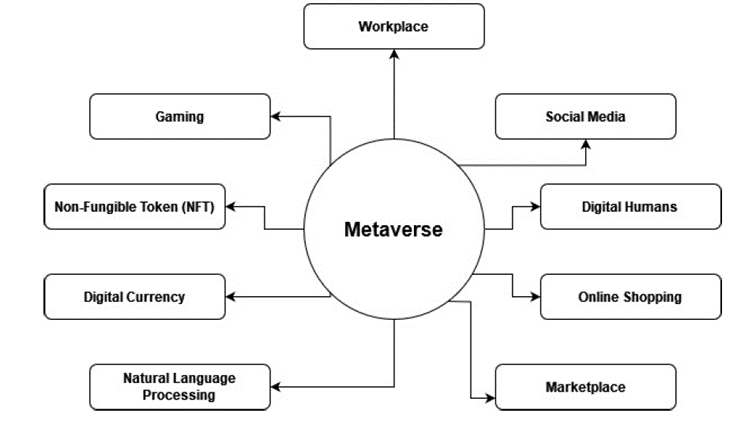
Figure 1: Mentions the various elements of the metaverse including popular trends in the current world scenario such as NFT’s (Non-Fungible Token), Digital Currency and much more.
“Metaverse” is something new and extraordinary for all the people, it is capable of enhancing comprehensive human development. This rapid development of the internet communication techniques and hardware platforms, combination of reality and virtuality, and Human computer interaction are the key characteristics of the Metaverse.[1] A metaverse is basically a collection of permanent, shared virtual space which is linked to both the digital as well as the physical world. People are able to access the metaverse as avatars which enables them to engage with each other.[2] Moreover from a perspective of media, Metaverse is an open-source platform closely associated to reality and a promising form of development when it comes to digital media.[3]
As we step into this new world, questions about ethics, privacy, and security becomes evident. The journey into the metaverse is in itself an experience to an adventure, where imagination has no boundaries. The metaverse represents not only a technological milestone, but also a cultural shift possessing the potential to redefine the very nature of our online existence.
Security Issues
Security issues in the metaverse are complex, given the interconnected and immersive nature of the virtual environments. As the metaverse keeps evolving, it presents several security challenges that needs to be addressed in order to assure safety, privacy, and integrity of data.
1. Identity and Authentication:
- Digital Identity Theft: In the metaverse, users are able to create digital personalities or avatars. Securing these virtual identities is very crucial to prevent theft, impersonation, and fraud.
- Authentication Challenges: Ensuring that the identity of the users and their security of the avatars is challenging. Biometric authentication and secure identity management systems are very important.
2. Privacy concerns:
- Persistent Data Collection: Metaverse has to collect vast amounts of data on user behaviour, their interactions and preferences. User may also me concerned about the data being used shared and monetized.
- Spatial Audio and Surveillance: Spatial audio technologies such as in VR can also capture personal conversations, raising surveillance concerns.
- Tracking and Profiling: The tracking of the user’s movement and their behaviour can lead to details user profiling.
3. Virtual Asset Security:
- Ownership and Transfer: The concept of owning virtual assets, such as NFTs, ends up raising questions about its ownership rights, transferring mechanisms, and asset security.
- Smart Contract Vulnerabilities: With the utilization of blockchain and smart contracts, vulnerabilities that my exist in the code can cause security breaches and impact one’s budget.
4. Content Moderation and Governance:
- Inappropriate content: Automated moderation of immersive content, which consists not just posts but the entire avatars, worlds, and other user-generated content, is not as straightforward as 2D audio-visual content.[4]
- Decentralized Governance: Decentralization is allowing the users to have more control over their virtual experiences. When it comes down to a decentralized metaverse, users possess ownership and control over their data, assets, and identities.
5. Access and Inclusivity:
- Accessibility: all of the necessary technology and features already exist for the most part. Thus, developers must continue to innovate in the metaverse while prioritizing its accessibility.
Mitigation of threats
Mitigating threats in the metaverse is essential to ensure the security, privacy, and well-being of users in this immersive digital environment. Here are strategies and best practices for threat mitigation in the metaverse:
1.Strong Identity and Authentication:
- Implementing robust identity verification methods in order to prevent and avoid unauthorized access to avatars as well as digital assets.
- Utilization of biometric authentication, multi-factor authentication (MFA), and secure identity management systems.
- Educating and spreading awareness to users about the importance of protecting their digital identity and using strong passwords
2. Privacy Protection:
- One of the ways is to limit the amount of personal information being shared on the platform. Users can also use the pseudonyms or avatars so as to protect their identity.
- Another way which can be used to protect privacy is to use privacy-enhancing technologies such as “encryption”.
- The threats to privacy can be broadly classified into two: Privacy based on data and the threats to privacy based on location.[5]
3. Cybersecurity Measures:
- Researching and standardisation efforts must be covering cybersecurity threats, in addition to this the physical and emotional damage to people which may result from the metaverse technology.[6]
4. Asset Security:
- Utilize blockchain technology to enhance the security of virtual assets like NFTs and digital currencies.
- Implement secure smart contracts to govern virtual asset ownership and transactions
- Rapid changes in the environments of technology, the protection of technologies has become more crucial.[7]
5. Continuous Monitoring and Adaptation:
- Continuously monitor the metaverse environment for evolving threats and vulnerabilities.
- Regularly update security protocols, policies, and technologies to adapt to changing threat landscapes.
Conclusion
The metaverse, with its limitless potential for immersive experiences and global connectivity, is undeniably a digital frontier worth exploring. However, the journey into this transformative realm comes with a set of intricate security challenges. These challenges encompass safeguarding digital identities, preserving user privacy, defending against cyber threats, and ensuring the security of virtual assets.
To navigate the metaverse securely, it is imperative to deploy robust identity verification measures, privacy-enhancing technologies, and advanced cybersecurity tools. Additionally, smart contract security and content moderation mechanisms must be in place to protect both digital assets and the well-being of users.
Since the Metaverse has enormous potential, its evolution depends on its ability to mitigate security threats. The journey into the metaverse is in its initial stages and is an ongoing one, but it is a journey that must be taken with utmost attentiveness and alertness in order to ensure the safety and security of this virtual realm.
References
- Metaverse in Education: Vision, Opportunities, and Challenges. (n.d.). Metaverse in Education: Vision, Opportunities, and Challenges | IEEE Conference Publication | IEEE Xplore.
- Security and Privacy Protection Obstacles with 3D Reconstructed Models of People in Applications and the Metaverse: A Survey. (n.d.). Security and Privacy Protection Obstacles With 3D Reconstructed Models of People in Applications and the Metaverse: A Survey | IEEE Conference Publication | IEEE Xplore.
- A Survey on the Metaverse: The State-of-the-Art, Technologies, Applications, and Challenges. (n.d.). A Survey on the Metaverse: The State-of-the-Art, Technologies, Applications, and Challenges | IEEE Journals & Magazine |
- Hine, E. (2023, June 16). Content Moderation in the Metaverse Could Be a New Frontier to Attack Freedom of Expression – Philosophy & Technology. SpringerLink.
- Location Privacy Protection Based on Differential Privacy Strategy for Big Data in Industrial Internet of Things. (n.d.). Location Privacy Protection Based on Differential Privacy Strategy for Big Data in Industrial Internet of Things | IEEE Journals & Magazine | IEEE Xplore.
- Protecting against cyber security threats in the metaverse. (n.d.). World Economic Forum.
- A proposed taxonomy of assets for information security risk assessment (ISRA). (n.d.). A Proposed Taxonomy of Assets for Information Security Risk Assessment (ISRA) | IEEE Conference Publication | IEEE Xplore.
- Deveci, M., Pamucar, D., Gokasar, I., Köppen, M., & Gupta, B. B. (2022). Personal mobility in metaverse with autonomous vehicles using Q-rung orthopair fuzzy sets based OPA-RAFSI model. IEEE Transactions on Intelligent Transportation Systems.
- Deveci, M., Pamucar, D., Gokasar, I., Köppen, M., Gupta, B. B., & Daim, T. (2023). Evaluation of Metaverse traffic safety implementations using fuzzy Einstein based logarithmic methodology of additive weights and TOPSIS method. Technological Forecasting and Social Change, 194, 122681.
- Gokasar, I., Pamucar, D., Deveci, M., Gupta, B. B., Martinez, L., & Castillo, O. (2023). Metaverse integration alternatives of connected autonomous vehicles with self-powered sensors using fuzzy decision making model. Information Sciences, 642, 119192.
- Upadhyay, U., Kumar, A., Sharma, G., Gupta, B. B., Alhalabi, W. A., Arya, V., & Chui, K. T. (2023). Cyberbullying in the Metaverse: A Prescriptive Perception on Global Information Systems for User Protection. Journal of Global Information Management (JGIM), 31(1), 1-25.
- Singla, A., Gupta, N., Aeron, P., Jain, A., Garg, R., Sharma, D., … & Arya, V. (2022). Building the Metaverse: Design Considerations, Socio-Technical Elements, and Future Research Directions of Metaverse. Journal of Global Information Management (JGIM), 31(2), 1-28.
- Gupta, B. B., & Sheng, Q. Z. (Eds.). (2019). Machine learning for computer and cyber security: principle, algorithms, and practices. CRC Press.
- Gupta, B. B., Perez, G. M., Agrawal, D. P., & Gupta, D. (2020). Handbook of computer networks and cyber security. Springer, 10, 978-3.
- Ahvanooey, M. T., Zhu, M. X., Li, Q., Mazurczyk, W., Choo, K. K. R., Gupta, B. B., & Conti, M. (2021). Modern authentication schemes in smartphones and IoT devices: An empirical survey. IEEE Internet of Things Journal, 9(10), 7639-7663.
Cite As
Hasan A. (2023) Preventing Metaverse Cyberattacks: Security issues and Threat Mitigation, Insights2Techinfo, pp.1