By: Shashank Shekhar Bhardwaj; Department of Computer Science & Engineering, CCET(Degree wing),Chandigarh, India Email:shashank1432004@gmail.com
Abstract
The rise of cloud computing, Internet of Things (IoT), and remote working models has led to the complete collapse of the usefulness of network security practices adopted before. This is due to the fundamental “Castle and Moat” concept in networking security, which relies on the assumption that all users within the network can be considered trusted. However, there are certain flaws in this approach because of the fact that after authenticating a user within the network, the user is considered a part of the trusted environment, which is vulnerable to many attacks. ZTA addresses this issue through the “Never Trust, Always Verify” principle…
Keywords: Zero Trust; Cybersecurity; Network Security; Authentication; Access Control
I. Introduction
The castle and moat approach was widely applied in the past for many years in business enterprises. It was an approach whose main feature involved setting up a fortress that consisted of a network border with high levels of security and internal traffic that was left unsecure. The network security was ensured using firewalls, Virtual Private Network (VPN) and Demilitarized Zone (DMZ). Passing through the network border would provide unlimited access into the network.[3] The approach was quite successful in corporate organizations due to minimal environments during the early stages of the internet usage. User access to the network had to be done behind company walls.
However, today’s business runs in a very different landscape, with cloud-based software, BYOD policies, remote workers, and the growing IoT network making it tough for us to define the borders that clearly mark the perimeters of the network. The hackers then take advantage of this confusion with insider threats, stealing of credentials, and later movement once they are within the premises of the network. Zero Trust Architecture, developed by NIST as part of their Special Publication 800-207,[2] is a revolutionary idea that takes into consideration all the requests to join the network as potentially risky and demanding of verification regardless of its source.
II. Security Threats in Traditional Networks
There are certain vulnerabilities associated with perimeter-based security approaches.[2],[3] Insider threats represent those types of threats where authenticated insiders having complete access rights exploit such access rights for stealing confidential data or causing harm to the infrastructure itself. It should be noted that the above-mentioned threat vector cannot be handled by perimeter security techniques alone. Hackers obtain necessary credentials either through phishing attacks or brute-force attacks and, thus, succeed in impersonating a legitimate user to bypass perimeter security.[6] Moreover, lateral movement techniques allow hackers to circumvent perimeter security and move across different locations within the network infrastructure. Finally, phishing campaigns lead users to surrender their passwords or download malicious code on their devices, making it difficult for perimeter security to handle such a threat vector.
III. Zero Trust Architecture: Concept and Principles
The Zero Trust security framework operates on the assumption that every access decision should abide by the rule “Never Trust, Always Verify.”[2],[3] In the zero trust model, there is no room for assuming anything without verifying it about any constituent of the system. Zero trust works on the premise that everyone, including users and devices and even the network itself, is assumed to be untrusted until proven otherwise. There are four fundamental principles on which Zero Trust Architecture is based.
Identity Verification operates on the assumption that all access requests are made through means of identity authentication using various methods such as certificates or Single Sign-On (SSO). Multi-Factor Authentication (MFA) contains additional measures that must be taken to access resources. MFA involves the knowledge, possession, and inherent properties of the user. Therefore, it becomes extremely difficult for any cybercriminal to steal the credentials. The principle of Least Privilege Access ensures that all systems and users have access to only the necessary minimum of privileges. Continuous Monitoring takes care of monitoring all sessions.
IV. Architecture of the Zero Trust Model
The Zero Trust model puts its principles into practice through a step-by-step access pipeline. You can see this in Figure 1 below.
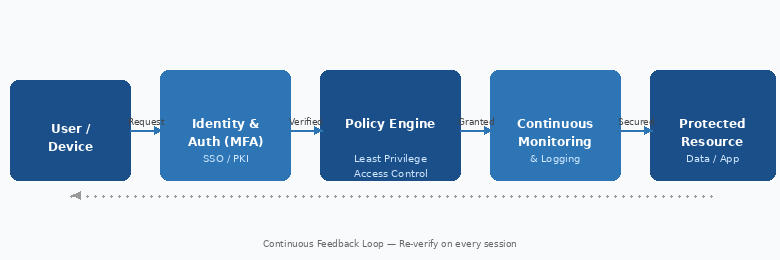
From a review of Figure 1, it will be clear that User/Device first makes a request to gain admission. The first recipient of the request is Identity & Authentication. At this stage, the credentials used for authentication are checked using either Multi Factor Authentication or Single Sign On Technology.[4] Once the credentials are verified, the request will then go through to the Policy Engine Layer. This is the stage where rules governing security are implemented to ensure that the user only does things that are important.[1],[2] When the request is cleared, the next step will involve accessing the Continuous Monitoring layer, where all activities performed by the User/Device are monitored on a constant basis.[6] This will take place over a stipulated period of time. Lastly, the User/Device will gain entry into the final destination which may consist of applications and databases. This will happen from a specific location only. The system monitors the behavior of the user or the device during its usage. The data collected in this process is passed to the Policy Engine. The Policy Engine uses this information to verify whether the user or the device is trustworthy. This is done throughout the period when the user or the device is connected to the system. Verification is performed first, followed by constant monitoring. The Policy Engine makes decisions based on this information.[2],[6]
V. Industry Applications
Moreover, the concept of ZTAs has been adopted globally in technology companies. The BeyondCorp architecture, which was proposed by Google following the hack operation referred to as “Operation Aurora” in 2009, removed reliance on traditional network-based Virtual Private Networks (VPNs). Instead, the system relied on the identity of devices and identities to authenticate users, becoming one of the practical examples of zero trust architecture.[4] The approach taken by Microsoft relies on identity management via Azure Active Directory, device protection with Intune, and threat intelligence with Sentinel.[5] In cloud-native environments, zero trust architectures are compatible with software-defined perimeters, containers, and Istio service meshes for microservice authentication.[1],[6]
VI. Challenges and Limitations
However, there are some challenges in deploying ZTA. The technical complexities associated with such a deployment should be taken into account, particularly regarding the redesign of the access control mechanism, the identity management framework, and the monitoring process in a large enterprise network that requires enormous manpower, skills, and cooperation.[1] Moreover, the financial cost associated with software license fees, training programs, and hardware upgrades is likely to become unmanageable for small organizations. Finally, the problem of employee pushback due to frequent authentication procedures like multifactor authentication, which may hinder their productivity, might create another hurdle.[1],[2]
VII. Conclusion
Zero Trust architecture is a natural evolution of the cyber security approach for enterprises. Since digital transformation makes the idea of having a definite network boundary irrelevant, trust-based systems become vulnerable to attacks and serve as the weak spot of the system.[2][3] Using the principle of “never trust, always verify” and combining continuous verification with microsegmentation and least privileges, Zero Trust can be considered one of the most efficient and dynamic approaches to enterprise security when facing such challenges as credential compromise, insider attack, and lateral movement.[6] As examples of success demonstrate, ZTA is scalable enough for practical application.[4][5] As far as future improvement, developments in AI-powered behavioral analysis and automation of policy management would simplify this process significantly
References
- Kumar, S., Singh, S. K., Aggarwal, N., Gupta, B. B., Alhalabi, W., & Band, S. S. (2022). An efficient hardware supported and parallelization architecture for intelligent systems to overcome speculative overheads. International Journal of Intelligent Systems, 37(12), 11764-11790.
- He, Y., Huang, D., Chen, L., Ni, Y., & Ma, X. (2022). A survey on zero trust architecture: Challenges and future trends. Wireless Communications and Mobile Computing, 2022(1), 6476274.
- Kindervag, J., Balaouras, S., Mak, K., & Blackborow, J. (2016). No more chewy centers: The zero trust model of information security. Forrester Research, 23.
- Ward, R., & Beyer, B. (2014). Beyondcorp: A new approach to enterprise security. login, 39(6), 6-11.
- Seaman, J. (2023). Zero trust security strategies and guideline. In Digital transformation in policing: The promise, perils and solutions (pp. 149-168). Cham: Springer International Publishing.
- Rose, S., Borchert, O., Mitchell, S., & Connelly, S. (2020). Zero trust architecture. NIST special publication, 800(207), 152.
- Mowloughi, A. (2024). A Cost-Effective Zero-Trust Approach for Cloud Computing: Experimental Evaluation on AWS Platform.
- Chandrashekar, P., & Kari, M. (2024). Design Machine Learning-Based Zero-Trust Intrusion Identification Models for Securing Cloud Computing System. Int. J. Res. Anal. Rev, 11(4), 901-907.
- Gupta, B. B., Gaurav, A., Marín, E. C., & Alhalabi, W. (2022). Novel graph-based machine learning technique to secure smart vehicles in intelligent transportation systems. IEEE transactions on intelligent transportation systems, 24(8), 8483-8491.
- Bhushan, K., & Gupta, B. B. (2017). Security challenges in cloud computing: state-of-art. International Journal of Big Data Intelligence, 4(2), 81-107.
Cite As
Bhardwaj S.S (2026) Zero Trust Architecture (ZTA) for Modern Cybersecurity, Insights2Techinfo, pp.1