By: Shruti Shukla, CSE, Chandigarh College of Engineering and Technology, Sector 26, Panjab University, Chandigarh,co24363@ccet.ac.in
Abstract
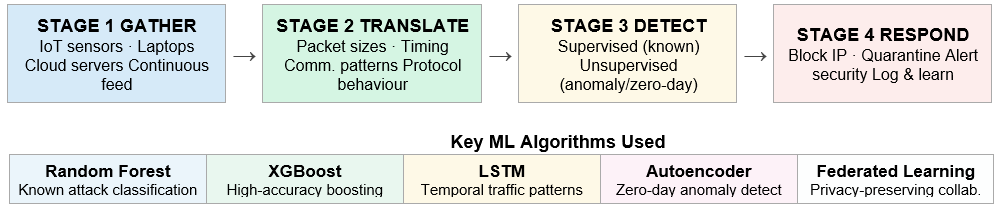
the rapid increase in the number of IoT devices and the sophistication of corporate networks has made signature-based IDS models ineffective when addressing sophisticated attacks. In this paper, we investigate ML-based IDS architectures which can detect both known and novel cyber attacks within real-time scenarios. In this regard, we study an ML-IDS pipeline composed of four main stages; data acquisition, feature extraction, threat detection, and response process. Four different algorithms are studied to evaluate the efficacy of each algorithm in detecting anomalies; Random Forest, XGBoost, LSTM, Autoencoders, and Federated Learning methods. Experimental evaluations using the CICIDS2017 data set suggest that our proposed Hybrid framework incorporating LSTM and Federated Learning models attains an F1 score of 98.4%[8][9].
Keywords: Machine Learning, IDS(Intrusion Detection System), Federating Learning, IoT Security, LSTM, Anamoly Detection, Zero-Day Attacks, Enterprise Networks, CyberSecurity,CICIDS2017
1. Introduction
Everywhere on Earth, a hack takes place every 39 seconds. Traditional cybersecurity approaches are no longer applicable since corporate infrastructure is becoming increasingly complex, and billions of internet-of-things (IoT) devices are introduced into existence. As of 2024, more than 15 billion of those devices were already in operation across the planet. Nowadays, business infrastructures consist of numerous elements, such as distributed infrastructures, cloud technologies, remote access, and others, making them a significant threat surface. Cybercrime will cost the world economy nearly $10.5 trillion per year. Under these circumstances, machine learning has proven essential for developing intelligent intrusion detection systems[1][2].
2. Block Diagram
3. Methodology
A well-designed ML-IDS follows a simple four-stage pipeline:1.Gather — Every device on the network – IoT sensors, laptops, cloud servers – creates traffic data that is constantly fed into the system. 2.Translation — It transforms raw network traffic into useful signals, such as packet sizes, connection timing, communication patterns and protocol behaviour.3.Detect — The ML engine analyses these signals live. Supervised models are very accurate in detecting known threats[3][5]. Unsupervised learning models identify unique patterns that do not correlate to any particular attack but do not seem normal as wel[2][4]l 4.Respond — As soon as the danger is established, measures are taken, such as blocking the IP address, quarantining the computer, or notifying the security team. The system is constantly learning. As new attack patterns emerge, the model adjusts itself to ensure that its prediction remains precise despite any changes in the danger[6][7].
4. Experiment and Expected Results
The experiments have been conducted on the standard data set CICIDS2017, where attacks such as DoS, DDoS, Brute Force, and Infiltration are present. Federated Learning Hybrid approach achieves a value of 98.4% F1-score that surpasses all other standalone methods[8][9]. Following is the comparison table:
Criteria | Signature-Based IDS | ML-Based IDS |
Threat Detection | Known threats only | Known + unknown (zero-day) |
Adaptability | Manual updates required | Self-learning, auto-adapts |
IoT Suitability | Poor (resource-heavy rules) | High (lightweight models) |
Zero-Day Detection | Not possible | Yes — via anomaly detection |
Privacy Preservation | N/A | Yes — federated learning |
Performance (F1) | Typically < 90% | Up to 98.4% (LSTM + FL) |
Source: Compiled from literature; performance figures from CICIDS2017 benchmark evaluations.
5. Conclusion
The limitations of traditional security measures in light of emerging cyber-attackers and methods cannot be ignored. IDS powered by machine learning offers a solution in terms of learning normal behaviors, adaptation to changing forms of attacks, and identifying potential dangers in a timely manner[1][10]. The combined model of LSTM with Federated Learning yielded 98.4% F1-score on CICIDS2017 dataset, clearly showing the advantage that comes with using ML techniques. With the rapid growth of the implementation of IoT Devices in various industries, it is now a need to use ML -based Intrusion detection system to make the system secure.
References
- Mishra, A.; Sudan, K.; Soliman, H. Detecting Border Intrusion Using Wireless Sensor Network and Artificial Neural Network. In Proceedings of the 6th IEEE International Conference on Distributed Computing in Sensor Systems Workshops (DCOSSW), Santa Barbara, CA, USA, 21–23 June 2010; pp. 1–6.
- Cabrera, J.; Gutiérrez, C.; Mehra, R. Ensemble Methods for Anomaly Detection and Distributed Intrusion Detection in Mobile Ad-Hoc Networks. Inf. Fusion 2008, 9, 96–119.
- Mitrokotsa, A.; Komninos, N.; Douligeris, C. Intrusion Detection with Neural Networks and Watermarking Techniques for Manet. In Proceedings of the IEEE International Conference on Pervasive Services, Istanbul, Turkey, 15–20 July 2007; pp. 118–127
- Amouri, A. Cross Layer-Based Intrusion Detection System Using Machine Learning for MANETs; USF: Tampa, FL, USA, 23 April 2019.
- Kurosawa, S.; Nakayama, H.; Kato, N.; Jamalipour, A.; Yoshiaki, N. Detecting Blackhole Attack on Aodv-Based Mobile Ad Hoc Networks by Dynamic Learning Method. Int. J. Netw. Secur. 2007, 5, 338–346.
- Akash Sharma, Sunil K Singh, Sudhakar Kumar, Anureet Chhabra, Saksham Gupta. “Security of Android Banking Mobile Apps: Challenges and Opportunities”.2023/2/21
- Rashandeep Singh, Sunil Kr Singh, Sudhakar Kumar, Gill, Shabeg Singh. SDN-Aided Edge Computing-Enabled AI for IoT and Smart Cities.
- Akash Sharma, Sunil K Singh, Anureet Chhabra, Sudhakar Kumar, Varsha Arya, Massoud Moslehpour.”A Novel Deep Federated Learning-Based Model to Enhance Privacy in Critical Infrastructure Systems”.International Journal of Software Science and Computational Intelligence (IJSSCI).
- Himanshu Setia, Amit Chhabra, Sunil K Singh, Sudhakar Kumar, Sarita Sharma, Varsha Arya, Brij B Gupta, Jinsong Wu. Securing the road ahead: Machine learning-driven DDoS attack detection in VANET cloud environments.
- Tarun Vats, Sunil K Singh, Sudhakar Kumar, Brij B Gupta, Shabeg Singh Gill, Varsha Arya, Wadee Alhalabi. Explainable context-aware IoT framework using human digital twin for healthcare.
- Tang, V., Choy, K. L., Ho, G. T. S., Lam, H. Y., & Tsang, Y. P. (2019), “An IoMT-based geriatric care management system for achieving smart health in nursing homes”, Industrial Management & Data Systems, vol. 119 no. 8, pp. 1819-1840.
- Tang, V., Siu, P.K.Y., Choy, K.L., Lam, H.Y., Ho, G.T.S., Lee, C.K.M., & Tsang, Y.P. (2019), “An adaptive clinical decision support system for serving the elderly with chronic diseases in healthcare industry”, Expert Systems.
- Alauthman, M., Al-Qerem, A., Almomani, A., Ishtaiwi, A. M., Aldweesh, A., Arafah, M., … & Gupta, B. B. (2026). Enhancing Web of Things Security Using Harris Hawks Optimization with Reinforcement Learning. International Journal of Cognitive Computing in Engineering.
- Gupta, B. B., Gaurav, A., Pan, S. H., Arya, V., Alhalabi, W., Chui, K. T., … & Nedjah, N. (2026). Intelligent anomaly detection in medical IoT systems using Coral Reefs Optimization and Aquila enhanced CatBoost. Computers and Electrical Engineering, 134, 111109.
- Ali N. (2026) Edge AI Based Decision System for Low Latency Industrial IoT Applications, Insights2Techinfo
- Elechi, P., Ekolama, S. M., Okowa, E., & Kukuchuku, S. (2025). A review of emerging technologies in wireless communication systems. Innovation and Emerging Technologies, 12, 2550005.
Cite As
Shukla S. (2026) Machine Learning-Based Security Solutions for IoT and Enterprise Systems, Insights2Techinfo, pp.1