By: Ritika Bansal, Insights2Techinfo, India Email: ritika@insights2techinfo.com
The realm of cloud computing has revolutionized the way businesses operate, offering scalability, flexibility, and efficiency. However, with these benefits comes a significant challenge: the threat of cyber attacks. In this digital age, cyber storms – a metaphor for sophisticated cyber threats – are becoming increasingly prevalent and potent, especially in cloud environments. This blog post explores the strategies and technologies that are pivotal in detecting and mitigating cyber attacks in cloud computing.
The Evolving Landscape of Cloud Security
Cloud computing, by its nature, presents unique security challenges. Data is not stored on-premises but in a remote server, accessible over the internet. This setup, while advantageous for accessibility and cost, opens up new avenues for cyber attacks. Understanding the types of threats – from data breaches and malware to DDoS attacks and insider threats – is the first step in building a robust defense mechanism[1-5].

Key Strategies for Cyber Attack Detection in Cloud Computing
1. Implementing Advanced Threat Detection Systems
Modern cloud security requires systems that can identify and respond to threats in real-time. Advanced threat detection systems, such as Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS), are essential. They monitor network traffic and user activities, identifying malicious patterns and anomalies indicative of a cyber attack.
2. Leveraging Artificial Intelligence and Machine Learning
AI and machine learning are game-changers in cyber security. These technologies can analyze vast amounts of data, learning and adapting to new threats over time. They can detect subtle anomalies that might elude traditional security measures, providing an additional layer of defense against sophisticated attacks[5-10].
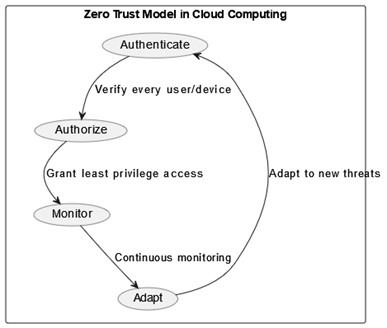
3. Adopting a Zero Trust Security Model
The Zero Trust model, based on the principle of “never trust, always verify,” is particularly effective in cloud environments. It involves strict identity verification for every person and device trying to access resources in a cloud environment, irrespective of whether they are within or outside of the network perimeter.
4. Regular Security Audits and Compliance Checks
Regular security audits and compliance checks ensure that the cloud infrastructure aligns with best practices and regulatory requirements. This proactive approach not only helps in identifying potential vulnerabilities but also ensures adherence to standards like GDPR, HIPAA, and PCI-DSS.
5. Encryption and Strong Authentication Protocols
Encrypting data at rest and in transit is crucial. Additionally, implementing strong authentication protocols, such as multi-factor authentication (MFA), adds an extra layer of security, ensuring that only authorized users gain access to sensitive data.
Emerging Trends in Cloud Security[10-14]
A. Security as a Service (SECaaS)
Security as a Service is a model where security services are delivered via the cloud. SECaaS offers scalable, flexible security management, including malware detection, intrusion detection, and more, without the need for extensive in-house resources.
B. Cloud Access Security Brokers (CASBs)
CASBs are security policy enforcement points placed between cloud service consumers and cloud service providers. They ensure that network traffic complies with the organization’s security policies, offering visibility, compliance, data security, and threat protection.
C. Automated Security Incident Response
Automation in incident response can significantly reduce the time and resources required to address security threats. Automated tools can not only detect but also respond to security incidents, mitigating risks promptly.
Best Practices for Cloud Security
Implementing the following best practices can significantly enhance cloud security[15-20]:
- Continuous Monitoring and Logging: Keeping an eye on all activities across cloud services to detect and respond to suspicious activities.
- Employee Training and Awareness: Educating staff about the latest cyber threats and good security practices.
- Data Backup and Recovery Plans: Regularly backing up data and having a robust disaster recovery plan in place.
- Regular Patch Management: Ensuring that all systems and applications are up-to-date with the latest security patches.
Conclusion
The battle against cyber storms in cloud computing is ongoing and dynamic. As cyber threats evolve, so must our strategies and tools for detection and mitigation. By leveraging advanced technologies, adopting best practices, and maintaining a culture of security awareness, organizations can fortify their cloud environments against the ever-changing landscape of cyber threats. The key to success lies in being proactive, vigilant, and continuously adapting to the new challenges that come with technological advancements.
References
- Singh, A., & Chatterjee, K. (2017). Cloud security issues and challenges: A survey. Journal of Network and Computer Applications, 79, 88-115.
- Kandukuri, B. R., & Rakshit, A. (2009, September). Cloud security issues. In 2009 IEEE International Conference on Services Computing (pp. 517-520). IEEE.
- Singh, V., & Pandey, S. K. (2014, October). A comparative study of cloud security ontologies. In Proceedings of 3rd International Conference on Reliability, Infocom Technologies and Optimization (pp. 1-6). IEEE.
- Krutz, R. L. (2010). Cloud security.
- Samarati, P., & De Capitani di Vimercati, S. (2016). Cloud security: Issues and concerns. Encyclopedia of cloud computing, 205-219.
- Mather, T., Kumaraswamy, S., & Latif, S. (2009). Cloud security and privacy: an enterprise perspective on risks and compliance. ” O’Reilly Media, Inc.”.
- Coppolino, L., D’Antonio, S., Mazzeo, G., & Romano, L. (2017). Cloud security: Emerging threats and current solutions. Computers & Electrical Engineering, 59, 126-140.
- Behl, A. (2011, December). Emerging security challenges in cloud computing: An insight to cloud security challenges and their mitigation. In 2011 World Congress on Information and Communication Technologies (pp. 217-222). IEEE.
- Paxton, N. C. (2016, November). Cloud security: a review of current issues and proposed solutions. In 2016 IEEE 2nd International Conference on Collaboration and Internet Computing (CIC) (pp. 452-455). IEEE.
- Sharma, S., Gupta, G., & Laxmi, P. R. (2014). A survey on cloud security issues and techniques. arXiv preprint arXiv:1403.5627.
- Mell, P. (2012). What’s special about cloud security?. It Professional, 14(4), 6-8.
- Kalaiprasath, R., Elankavi, R., & Udayakumar, R. (2017). Cloud security and compliance-a semantic approach in end to end security. International Journal on Smart Sensing and Intelligent Systems, 10(5), 482-494.
- Nassif, A. B., Talib, M. A., Nasir, Q., Albadani, H., & Dakalbab, F. M. (2021). Machine learning for cloud security: a systematic review. IEEE Access, 9, 20717-20735.
- Hendre, A., & Joshi, K. P. (2015, June). A semantic approach to cloud security and compliance. In 2015 IEEE 8th International Conference on Cloud Computing (pp. 1081-1084). IEEE.
- Khan, N., & Al-Yasiri, A. (2016). Identifying cloud security threats to strengthen cloud computing adoption framework. Procedia Computer Science, 94, 485-490.
- Gupta, B. B., Gupta, S., Gangwar, S., Kumar, M., & Meena, P. K. (2015). Cross-site scripting (XSS) abuse and defense: exploitation on several testing bed environments and its defense. Journal of Information Privacy and Security, 11(2), 118-136.
- Gaurav, A., Gupta, B. B., & Panigrahi, P. K. (2023). A comprehensive survey on machine learning approaches for malware detection in IoT-based enterprise information system. Enterprise Information Systems, 17(3), 2023764.
- Poonia, V., Goyal, M. K., Gupta, B. B., Gupta, A. K., Jha, S., & Das, J. (2021). Drought occurrence in different river basins of India and blockchain technology based framework for disaster management. Journal of Cleaner Production, 312, 127737.
- Gupta, S., & Gupta, B. B. (2016). XSS-SAFE: a server-side approach to detect and mitigate cross-site scripting (XSS) attacks in JavaScript code. Arabian Journal for Science and Engineering, 41, 897-920.
- Ahvanooey, M. T., Zhu, M. X., Li, Q., Mazurczyk, W., Choo, K. K. R., Gupta, B. B., & Conti, M. (2021). Modern authentication schemes in smartphones and IoT devices: An empirical survey. IEEE Internet of Things Journal, 9(10), 7639-7663.
Cite As
Bansal R. (2023), Battling Cyber Storms: Strategies for Effective Attack Detection in Cloud Computing, Insights2Techinfo, pp.1