By: Pooja
XSS attack can be classified into 3 main categories: Stored, Reflected and, DOM-based XSS attack. In this article, you will learn about the DOM-based XSS attack.
DOM-based XSS Attack: Document Object Model (DOM) is a platform that enables web page processing and manipulation inside a web browser. Unlike Stored and Reflected XSS attacks that are considered server-side XSS attacks, a DOM-based XSS attack is a client-side XSS attack. It is triggered only when the client-side scripts modify the structure of the DOM tree by the data provided by the user. If this data is not appropriately handled, an attacker may exploit this feature to fulfill its intentions. Here, the injected malicious payload is never stored in the database of the website. It means server logs have no information about this attack, making it more difficult to identify this attack at the server-side with the help of any firewalls, filters, etc.
This kind of vulnerability emerged when JavaScript shifts data from vulnerable sources like DOM URL to the sink where dynamic code implementation is completed, such as eval() and innerHTML() methods. So, the attacker is only required to search for such sources to inject a malicious payload that passes to sink and causes malicious script execution.
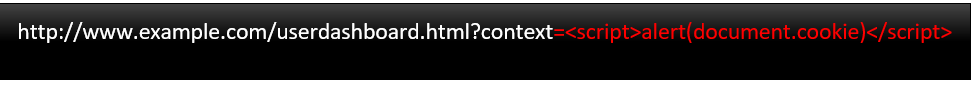
DOM properties such as window.location(), document.location(), document.anchors(), document.write() are some of the properties of the DOM tree exploited by an attacker to launch this type of XSS attack. Here, the attacker crafts a link and sends it to the victim. When the victim clicks on the link, the website will generate the response that gets executed inside the victim’s browser. Here, malicious code is not directly embedded in the response, but the execution of legitimate response code triggers the execution of the malicious attack payload. This action satisfies the evil intentions of the attacker. Below are the steps are given to execute the DOM XSS attack:
- The attacker crafts a URL with the malicious code and sends it to the victim through a message or any other method.
- The victim clicks on the link and makes a request to the website.
- The website will generate the static HTML response and send it to the victim.
- The victim’s browser renders the response web page that will eventually trigger malicious code using document.URL property. This will cause a DOM XSS attack.
In this XSS category, we can notice the following points:
- The generated response page is static and does not include the malicious attack payload, unlike the other 2 categories of XSS attack categories.
- Server-side identification and mitigation tools cannot shield against DOM-based XSS attacks as the server has no information of the illicit attack payload.
Related Articles
- Reflected XSS attack. What is Cross-Site Scripting? XSS Cheat Sheet | Veracode
- Stored XSS attack. The Ultimate Guide to Stored XSS Attacks – Hashed Out by The SSL Store™.
Thanks , I have recently been searching for information approximately this topic for a long time and yours is the greatest I have discovered so far.