By: Arya Brijith, International Center for AI and Cyber Security Research and Innovations (CCRI), Asia University, Taiwan,sia University, Taiwan, arya.brijithk@gmail.com
In this article, we shall discuss -Firewalls. A firewall serves as a border or protective barrier in cybersecurity between reputable internal networks and dubious external networks. It functions as a security mechanism that uses pre-established security principles to regulate and keep an eye on incoming and outgoing communication patterns.
Keywords firewall, cybersecurity, threats, internet, data packets, performance
Introduction
The primary purpose of a firewall is to prevent unauthorized connections from entering or exiting the private network while permitting authorized ones to get through. It functions by keeping an eye on data packets as they move between networks. Data packets are examined concerning pre-established guidelines or specifications, including IP addresses, port numbers, or keywords unique to a given protocol. The firewall decides whether to accept or deny data packets based on these criteria. This real-time decision-making process assists in defending against a range of online dangers, such as malware, illegal access attempts, denial-of-service (DoS) assaults, and other such threats.
Types of Firewalls
There are many different types of firewalls, each with its security and performance. Let us discuss about few of them.
- Packet Filtering Firewall: Data packets are filtered using the packet filtering firewall approach when they travel via a router or switch. It filters packets according to pre-established criteria, including protocols, ports, source and destination IP addresses, and more. It performs admirably, but it is limited in its functionality and is vulnerable to more complex assaults.
- State Monitoring Firewall: This firewall keeps an eye on packets at the network and transport levels as well as the state of active connections. It evaluates the traffic and decides if it is suitable based on the junction data. Because it can remember the state of connections, it is more secure than packet filtering.
- Proxy firewall: This firewall blocks both inbound and outbound traffic while serving as a gateway between the internal and external networks. By acting as a middleman and carefully reviewing every packet to ensure that only secure data is transmitted, it improves security but occasionally degrades speed owing to heavy usage.
- Application-aware firewall: This sophisticated firewall offers more precise traffic management by functioning at the OSI model’s application layer. It can more effectively prevent application-specific attacks by identifying certain programs or services and keeping track of their usage.
- Next-Generation Firewall (NGFW): NGFW incorporates cutting-edge technologies like deep packet inspection, SSL inspection, and intrusion prevention with characteristics found in classic firewalls. With its remarkable edge, it offers a comprehensive security solution that can identify and thwart attacks in real-time.
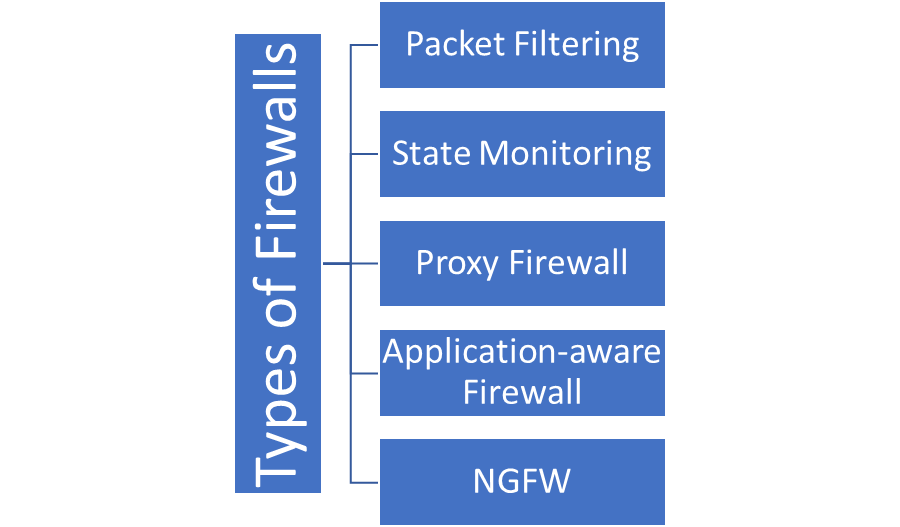
Figure 1: Types of FirewallsConclusion
Firewalls are essentially the unquestionable protectors of critical networks and data repositories against potential breaches and assaults. They represent the first line of protection against an ever-evolving array of cyber threats.
References
- Liang, J., & Kim, Y. (2022, January). Evolution of firewalls: Toward securer network using next generation firewall. In 2022 IEEE 12th Annual Computing and Communication Workshop and Conference (CCWC) (pp. 0752-0759). IEEE.
- Anwar, R. W., Abdullah, T., & Pastore, F. (2021). Firewall best practices for securing smart healthcare environment: A review. Applied Sciences, 11(19), 9183.
- Hermansson, L., Lundberg, A., Gruber, S., Jolly, A., Lind, J., Righard, E., & Scott, H. (2022). Firewalls: A necessary tool to enable social rights for undocumented migrants in social work. International Social Work, 65(4), 678-692.
- Deveci, M., Pamucar, D., Gokasar, I., Köppen, M., & Gupta, B. B. (2022). Personal mobility in metaverse with autonomous vehicles using Q-rung orthopair fuzzy sets based OPA-RAFSI model. IEEE Transactions on Intelligent Transportation Systems.
- Chopra, M., Singh, S. K., Gupta, A., Aggarwal, K., Gupta, B. B., & Colace, F. (2022). Analysis & prognosis of sustainable development goals using big data-based approach during COVID-19 pandemic. Sustainable Technology and Entrepreneurship, 1(2), 100012.
- Zulkefly, N. A., Ghani, N. A., Hamid, S., Ahmad, M., & Gupta, B. B. (2021). Harness the global impact of big data in nurturing social entrepreneurship: A systematic literature review. Journal of Global Information Management (JGIM), 29(6), 1-19.
- Gupta, B. B., & Lytras, M. D. (2022). Fog-enabled secure and efficient fine-grained searchable data sharing and management scheme for IoT-based healthcare systems. IEEE Transactions on Engineering Management.
Cite As
Brijith A. (2023) Firewalls in Cybersecurity, Insights2Techinfo, pp.1