By: A. Sethi, K. T. Chui, K. Yadav, A. A. El-Latif
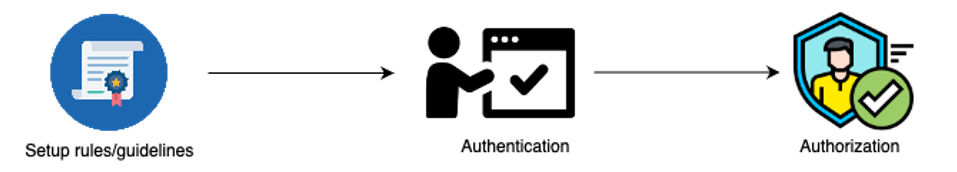
As technology has advanced, so have the methods in which computer networks are being attacked. According to RiskBased Security research, in the first three quarters of 2020 alone, over 36 billion records were breached. Although this 51% decrease in the number of breaches, it is still pretty high [1]. Hence, it is essential for a user to protect its computer system from all kinds of threats. Security can be enforced using two subgroups of measures – using security policies and using an architecture that enhances the security of a network [2]. The central concept of computer security is access control. Figure 1 represents three steps to monitor which user has access to what information. The first step is laying down fundamental rules of principle security policies that should be kept in mind while providing access to an interested party. These rules and policies need to be elaborate such that they provide a detailed as well as clear frame of instructions that can further be used for granting or denying access. These rules are designed to protect the integrity and confidentiality of the data [3]. The next two steps – authentication and authorization, are key for any provision of access. Authentication is the process in which the party who requests access to a resource is verified. This step confirms that the interested party is not malicious and should be allowed access to requested resources as per the previously set guidelines. Once the party is proven to be authentic, the last step is to grant or revoke the access of the resources to the requester.
The security of a computer system is concerned with the operating system, commercial and internet security [4].
Operating System Security – The two policies that stand out in operating system control are discrete and mandatory access control policies. Mandatory access control provides control to users based on hierarchy, confidentiality level, and user clearance level. These policies are usually granted in bulk to different hierarchical groups. On the other hand, discrete access control provides access to certain specific resources or permission to specific groups or individuals.
Commercial Security – Access to database records, foreign keys, commercial files, and programs can be given partial or full control. e.g., one group is given only the right to perform a set of operations on a database. Other segregation of control based on job profiles and positions in an organization can be done with the help of role-based access. This enables the division of users into groups that are granted bulk permissions.
Federated access control – A federated structure is a hybrid of management of identities, credentials, policy rules, and decisions. In this type of access control, the digital identities of users of a federation are monitored and managed under one system.
Internal security – Perhaps one of the most efficient ways of controlling an organization’s security is managing what information is allowed and sent through the internet. Firewalls and intrusion detection systems should be established to prevent attacks. The organization should establish strict rules that prevent users from accessing suspicious websites and email spam.
Other aspects of computer security are code-based, memory-based, software security, and access control.
Some of the methods that are already in practice and some of the new technologies that are being developed on top of them have been discussed briefly below –
1. Cryptography – Cryptography is the most researched and developed concept when it comes to computer security. It involves converting legible data to an illegible format. The data shall be converted back to its original format only after the user is authenticated and a private key is provided to do the same. Over the years, the simple encryption technique has evolved into many methods that can be used to protect the security of a computer network. Currently, the most popular forms of cryptography are – symmetric encryption, public-key encryption, and hash functions. Further concepts like elliptic curve cryptography, visual cryptography, and quantum cryptography are also being developed on the previously mentioned cryptography concepts.[5]
2. User Authentication [6] – Cryptography techniques are developed to authenticate a legitimate user and prevent information leakage from attackers. Popular authentication techniques are two-way authentication and dynamic biometric-related schemes. As the name suggests, a two-way password utilizes two steps to authenticate a user. The first step is generally a password setup and provided by the user. The second step is a security token or biometric factors like fingerprints and facial scans that authenticate the user. The security tokens are provided in such a way that they last for a short period of time and/or are circulated regularly. This is an improvement compared to a single-step authentication process, as two-way authentication makes it harder for attackers to access information.
References
[2] https://www.ekransystem.com/en/blog/mac-vs-dac
[3]Landwehr, C.E. Computer security. IJIS 1, 3–13 (2001). https://doi.org/10.1007/s102070100003
[4] Gollmann, Dieter. “Computer security.” Wiley Interdisciplinary Reviews: Computational Statistics 2.5 (2010): 544-554.
[5] Lara, Pablo Daniel Marcillo, et al. “Trends on computer security: Cryptography, user authentication, denial of service and intrusion detection.” arXiv preprint arXiv:1903.08052(2019).
[6] https://searchsecurity.techtarget.com/definition/two-factor-authentication
[7] Fulton, K. R., Gelles, R., McKay, A., Abdi, Y., Roberts, R., & Mazurek, M. L. (2019). The effect of entertainment media on mental models of computer security. In Fifteenth Symposium on Usable Privacy and Security ({SOUPS} 2019) (pp. 79-95).
[8] Stallings, W., Brown, L., Bauer, M. D., & Bhattacharjee, A. K. (2012). Computer security: principles and practice. Upper Saddle River, NJ, USA: Pearson Education.
[9] Littlewood, Bev, Sarah Brocklehurst, Norman Fenton, Peter Mellor, Stella Page, David Wright, John Dobson, John McDermid, and Dieter Gollmann. “Towards operational measures of computer security.” Journal of computer security 2, no. 2-3 (1993): 211-229.
Cite this article:
A. Sethi, K. T. Chui, K. Yadav, A. A. El-Latif (2021), Computer Security. Insights2Techinfo, pp. 1
Very Informative
Thank you