By: U. Yadav
Technological advances endanger cybersecurity. Indeed, the latest developments in defense practitioners’ defensive techniques feel a sense of loss. In addition, the intensity and amount of cyber threats have escalated as defensive strategies and technologies operate in a never-ending loop. Security researchers provide excellent tools to protect insecure information and systems against cybercriminals by integrating the power of artificial intelligence with cryptography [1]. It delivered instant insights after introducing such engineering, resulting in slower reaction times. Protecting a piece of information is quite complicated than before. There is no guarantee that the data or information is authenticated and breach-proof by upgrading existing cybersecurity technologies and applying any applicable protection layer. But the role of security practitioners will be eased by robust funding for advanced technologies [4].
The advancement of information technology can enable a machine to behave and reason like just a human being. Intelligence is a unique feature of software development that necessitates a computer that responds and functions in the same way as a conscious imagination. The comparison of human perception is one of the main aspects of AI technology. The computer is responsible for identifying sensation and voice as characteristics that may be inserted into the system that utilizes a typical living scenario without human intervention. On the other hand, AI technology is the analysis of intellectual skills’ entities that reflects the state of the environment and effectively accomplishes their purpose. The bulk of programs in the computer industry were designed to serve specific objectives based on the problem’s structure and the use of distinguishing characteristics obtained from human elements’ inherent existence.
Defense from Cyber Threats Using Artificial Intelligence:
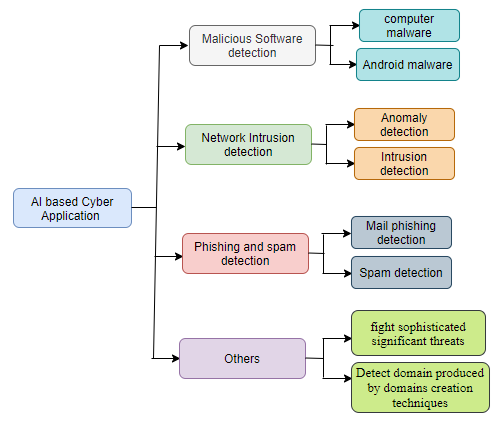
Several strategies have already been suggested that use the Artificial Intelligence approach to detect or categorize cyber-attacks, including malicious software, network attacks, scamming, and spamming assaults, fight sophisticated significant threats; and detect domains produced by domains creation techniques. We describe the details regarding classification of cyber-attacks into several classes such as malicious software detection, network intrusion detection, phishing and defacement detection, and others, including significant sophisticated threats and identifying malicious domain assault threats. The main areas of using AI for cybersecurity are described in Figure 1.
AI technology is a term used to describe a group of individuals who use problem-solving strategies to improve comprehend high-level activities in the functioning of conscious aspects, choice, and the psychological process. In contrast to general brains, AI technology is an intellect generated by machines [3, 2].
Employing different techniques and strategies to guarantee that technologies are secured against risks and attacks and offer individuals adequate and precise operations exposes cyber security. As a result, the information security discussed in this article encompasses both external and internal risks. Such attacks would have a significant impact on the structures’ normal operating conditions, so cyber security’s primary objective is to preserve chances as often as potential, as well as to satisfy the expectation of identification in front of an incident that occurred, trying to handle during an unfortunate incident, and recovering after such a regrettable incident efficiently and accurately.
To begin with, combining various Intelligence approaches in a defensive strategy might still be a promising research area. For example, incorporating microbial computing with machine learning and deep learning techniques yields good results in detecting attacks for monitoring the network infiltration. As a result, while the variety of microbiological methods used in security has still been restricted, combining different approaches is a promising area of research. Secondly, the connection between organizational intelligence and robots in cyber security should be investigated. The bots will accomplish the work independently in this human-machine approach, with humans just being able to oversee and interfere whenever needed.
Open research Issues and challenges:
- AI-based techniques in a defense solution
- Human intellect and machines for cyber defense
- Intelligent Antivirus software for security
- Algorithmic developments and applications of machine learning and data mining for Big Data.
References
- M H Jarrahi Artificial intelligence and the future of work: human-AI symbiosis in organizational decision making Business Horizons, issue 4, p. 577 – 586 Posted: 2018
- Rahul Reddy Nadikattu “Implementation of New Ways of Artificial Intelligence” in Sports Journal of Xidian University, Volume 14, Issue 5, 2020, Page No: 5983 – 5997 15 Pages · Posted: 10 Jun 2020.
- Amberkar A, Awasarmol P, Deshmukh G, Dave P (2018) Speech recognition using recurrent neural networks. In: 2018 international conference on current trends towards converging technologies (ICCTCT), pp 1–4.
- Bao H, He H, Liu Z, Liu Z (2019) Research on information security situation awareness system based on big data and artificial intelligence technology. In: 2019 international conference on robots intelligent system (ICRIS), pp 318–322
Cite this article:
U. Yadav (2021) Intelligent Advancement Technology in Cyber Security, Insights2Techinfo, pp. 1
Very informative and interesting work
Very nice article.
Very Informative
Thank you
Informative Work!
Thank you