By: V. Adat
The fifth-generation and beyond (B5G) networks and services are being characterized by strict requirements regarding throughput gain and energy consumption. This evolution of wireless mobile networking towards higher data rates and capacity (eMBB), ultra-low latency, and increased resilience (URLLC) is fueled by the rapid penetration of advanced smart mobile applications and their diverse nature in terms of quality of experience, security, and ubiquity. Specifically, the future networking environment will be characterized by highly dense heterogeneous cells, a massive Machin Type Communication (mMTC) use case. This heterogeneity is extended to the diverse radio access technologies that 5G networks will incorporate (i.e., 3G, 4G, 5G, etc.) as well as the different types of cells that future wireless networks will consider, including macro, pico, and small cells. As the future networking environment begins to materialize, it seems that the concept of cooperated small cells may provide a basis for the mobile cell architecture. The 5G paradigm, as it emerges in recent studies and early pilots, adopts several technological solutions to form the building blocks of the next-generation wireless mobile network architecture and address all these challenges and designed with these three target services (eMBB, URLLC, and mMTC) being the three corners of the 5G triangle [1]. Towards this end, Network Coding (NC) by incorporating either linear or non-linear coding schemes is being considered as a key enabler for achieving the requirements for increased throughput and high resilience for wireless mobile networks. Moreover, different theoretical and practical studies regarding NC points out other advantages such as low latency and improved security making it a multi-faceted key enabler for the next-generation wireless networks.

Even though the underlying concepts of network coding were discussed in the research community as early as 1978 [2], the idea became more popular with the seminal paper of Ahlswede et al. [3] which discussed the advantages of linear network coding with the famous butterfly example. Network coding in simple words is the concept of coding multiple information flows or packets together. In the case of a multi-hop network, the intermediate nodes recode the packets instead of the simple store-and-forward approach used in traditional routing. Contrary to general forward error correcting (FEC) codes where coding happens only at the source and destinations, NC allows all the intermediate nodes the capacity to recode the packet. Further studies on NC explored different areas related to the basic concept of mixing information flows to achieve near-optimal bandwidth efficiency and proposed different protocols. Among the most discussed NC paradigms, random linear network coding (RLNC) [4] has gained significant interest from the research community. In RLNC, the native packets are coded with random coefficients and it provides highly reliable, robust, stateless coding making it the most suitable for wireless environments. Furthermore, it can also achieve low latency and introduce some erasure correction to cope up with channel losses. Network coding has found applications in multiple scenarios, such as content distribution, multipath TCP, multi-hop communications, etc. In this article, we discuss a few interesting use cases of NC and discuss some of the most interesting features.
Cooperative Content Distribution
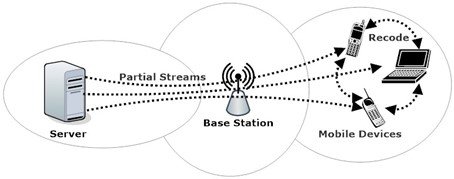
One of the initial applications of NC in practical implementations was a cooperative distributed storage proposed by Microsoft [5]. In a distributed storage system, data is often stored as sectors distributed to multiple storage units. This setup usually needs a high level of redundancy to ensure successful availability all the time. If we deploy RLNC, instead of storing independent sectors, randomly coded sectors can be stored at the storage unit and any n number of such coded sectors can be used to reconstruct the required information. This can effectively reduce the number of additional sectors to be stored, as any coded sector can replace any missing sector and there is no need to duplicate any particular sector [6]. This is the case of storing large content with applications like multi-cloud, storage area networks and edge caching and a reverse analogy can be used for content distribution as well. Let’s consider a scenario of a sports arena in the 5G era with a group of people streaming the same football match or playing a video game. These people are streaming the same content, however in traditional network three different information flows caters them. However, if we can also utilize the WiFi connection they share or enable D2D communication between these people, the server can send part of the content to each player using LTE and they cooperate between them to share the content and get the complete picture! This beautiful idea can be achieved efficiently, coping up with the channel losses, using RLNC. Instead of distinct packets, coded packets can be sent to each participant and any n packet can be used to get the complete information. Such NC-enabled cooperative networks can improve the bandwidth usage and improve the reliability of the network, as shown in Figure 2 [7].
Low Latency Communication Networks
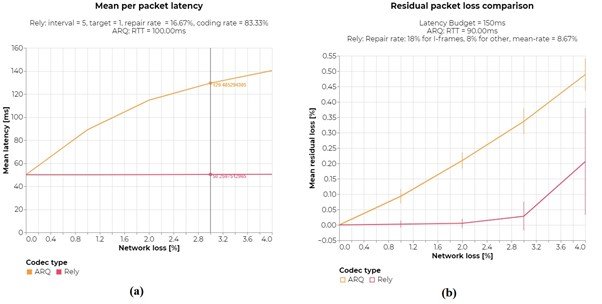
The above discussed content distribution network itself shows the advantage of RLNC in multi cast communication, but the benefits are not only limited to bandwidth efficiency. RLNC can also be used to realize low latency communication in multipath scenarios, even in a single hop connection with a lossy channel. One of the major advantages of network coding that makes it better than the traditional TCP environment is the randomness of packets. In TCP the sequencing of packets is very important and at the receiver, packets need to be reached in order. However, packet losses are very common and this will require retransmissions of exactly those packets which are lost in the channel. For example, if ARQ is used, this can only happen when the sender does not receive the acknowledgment regarding a packet, thus increasing the overall latency to a minimum of three times the link latency. Furthermore, all the packets from the missing one must be retransmitted to satisfy the sequencing in TCP. The well-known error correcting schemes can address the issue of packet loss by either adding a large amount of redundancy (bandwidth inefficient) or incurring a large latency. However, RLNC can play a vital role in achieving low latency without wasting bandwidth. Here, the packets are coded with random coefficients and the reception of a sufficient number of linearly independent packets can ensure a successful reception of the complete information. The order of the packets is not significant as any packet can substitute another one. For example, if there are 10 packets to send and suppose the 5th one is lost and it is identified by the source while sending the 8th packet. In normal TCP all packets from the 5th need to be sent again and another instance of packet loss will further increase the number of transmissions and latency. On the other hand, in RLNC, even if the 5th coded packet is missing, the next one can substitute it and as soon as the receiver gets the 11th coded packet, 10 linearly independent coded packets have reached the destination and it can easily be decoded to get complete information. Here not only the number of transmissions is reduced, but also the latency is decreased as the sender can even pre-emptively send additional packets accounting for the packet loss. In practical examples demonstrated by Steiwurf’s Rely [8], a next-generation FEC based on RLNC technology outperforms ARQ and achieves high-quality transmission with low latency, making it the most suited choice for SD-WAN providers. Figure 3 shows a comparison of Rely with ARQ for mean latency and residual packet loss (when the maximum latency is defined) against network loss, as presented in their latest blog [9].
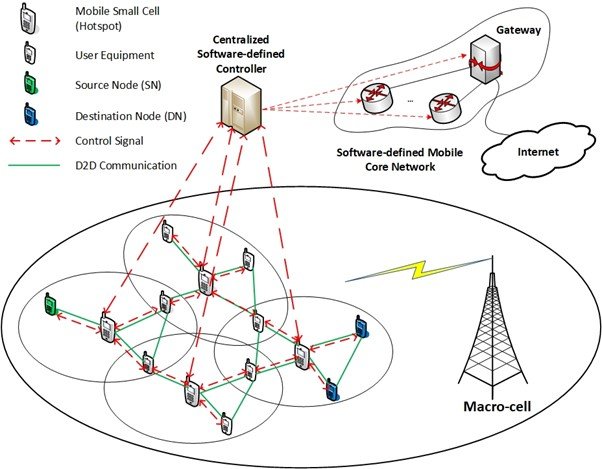
The advantage of RLNC is not limited to single-hop communications. Rather it is more powerful in multi-path, multi-hop environments. H2020-MSCA-ITN-SECRET [10] is an EU-funded project that explored the possibility of NC-enabled mobile small cells to cater to the requirements of future wireless networks. The general architecture envisioned by SECRET, as in Figure 3 shows how NC can be used in the 5G and beyond networks with an example of an MP-MH communication network with D2D communications and all end devices using RLNC to improve the bandwidth efficiency and reliability. Furthermore, decreasing the number of transmissions will also help to reduce the power consumption and energy efficiency is a major concern with a large number of devices and continuous data traffic in the modern world. NC also makes the network more energy efficient by reducing power consumption as well.
Secure Network Coding
Security is an important concern in the digital world. As technology evolves, security threats also have increased significantly. The case is not different with network coding. The core concept of network coding, mixing of packets at intermediate nodes, can lead to a security threat called pollution attack as the intermediate nodes have more freedom to play with the packets in transition, and a malicious user can exploit it to pollute the network. If a malicious adversary is acting as an intermediate node in an NC-enabled environment, instead of recoding genuine packets, it can also inject a polluted packet into the network. If such polluted packets are not detected at the earliest hop, it can further spread across the network and the effect will be catastrophic as more information flows will get corrupted. Figure 4 shows how a polluted packet can spread across the network. A variety of integrity schemes have been proposed by the research community to prevent pollution attacks. Generic cryptographic integrity schemes such as signatures or message authentication codes (MACs) can not suit the requirement of network coding as the packets are frequently coded while transmission and the packets are not the same during transmission. Thus integrity schemes for RLNC also need to satisfy homomorphic property on RLNC operations. The basic requirement for such schemes is that they should be able to verify the integrity of packets even if linear mathematical computations are performed over the packets. Such homomorphic integrity schemes are designed for NC-enabled environments, where [11], [12] are a few recent homomorphic MAC-based integrity schemes designed for secure NC-enabled next-generation wireless networks.

Even though network coding introduces some security challenges such as pollution attacks, it also has some inherent security features that are very useful, especially against eavesdropping. Since the packets are always coded, an eavesdropper with limited listening capacity will have no benefits in NC-enabled environments. Unless the attacker can listen to all coded packets (sufficient number to decode the packets), it can not get any meaningful information from overhearing. In a multipath environment where coded packets are sent through different channels, if an adversary listens to only one (or limited number of) channel(s), it can never get enough packets to decode the message and overhearing will not leak any part of the message directly. On the other hand, strong encryption of a single channel can be as efficient as encrypting all the channels since the information sent through the encrypted channel is a must to decode the message successfully. This can even inspire post-quantum cryptosystems as discussed in [13]. Thus network coding can also be used in future applications to achieve security, making it the perfect multi-faceted enabler for next-generation wireless networks.
These are only some of the interesting use cases of network coding. Researchers and industrial experts around the globe are actively exploring the future aspects of the technology as well as developing products making use of RLNC. The applications of RLNC vary from distributed storage, content delivery, low latency communication, 5G and IoT environments, multi-cloud environments, satellite communications, and many more. As we head to a world of densely networked digital devices, network coding tries to harness the best of the available resources reliably, securely, and efficiently. Some of the recent research trends and future aspects in this area are:
- NC-enabled 5G and beyond networks
- Multicast applications for IoT/ firmware/ content updates
- Automated and connected traffic environments
- Applications of network coding in MP TCP
- Explore the security aspects of network coding for a post-quantum era
- Explore inter-flow network coding and hybrid coding opportunities
References
[1] M. Agiwal, A. Roy, and N. Saxena, “Next generation 5G wireless networks: A comprehensive survey,” IEEE Commun. Surv. Tutorials, vol. 18, no. 3, pp. 1617–1655, 2016.
[2] M. Celebiler and G. Stette, “On increasing the down-link capacity of a regenerative satellite repeater in point-to-point communications,” Proc. IEEE, vol. 66, no. 1, pp. 98–100, 1978.
[3] R. Ahlswede, N. Cai, S.-Y. Li, and R. W. Yeung, “Network information flow,” IEEE Trans. Inf. theory, vol. 46, no. 4, pp. 1204–1216, 2000.
[4] T. Ho et al., “A random linear network coding approach to multicast,” IEEE Trans. Inf. Theory, vol. 52, no. 10, pp. 4413–4430, 2006.
[5] C. Gkantsidis and P. R. Rodriguez, “Network coding for large scale content distribution,” in Proceedings IEEE 24th Annual Joint Conference of the IEEE Computer and Communications Societies., 2005, vol. 4, pp. 2235–2245.
[6] “Storage Solutions: Code On Technologies.” (accessed Sep. 09, 2021).
[7] V. Adat Vasudevan, C. Tselios, and I. Politis, “On Security Against Pollution Attacks in Network Coding Enabled 5G Networks,” IEEE Access, vol. 8, pp. 38416–38437, 2020.
[8] Steinwurf, “Rely: Next Generation FEC to the rescue.” (accessed Sep. 09, 2021).
[9] Steinwurf, “Benchmarking Steinwurf’s FEC for SD-WAN Service Providers without an integrated FEC solution.” (accessed Sep. 09, 2021).
[10] J. Rodriguez et al., “SECRET – Secure network coding for reduced energy next generation mobile small cells: A European Training Network in wireless communications and networking for 5G,” in 2017 Internet Technologies and Applications (ITA), 2017, pp. 329–333.
[11] V. Adat, I. Politis, C. Tselios, and S. Kotsopoulos, “Secure Network Coding for SDN-Based Mobile Small Cells,” in International Conference on Broadband Communications, Networks and Systems, 2018, pp. 347–356.
[12] V. Adat, I. Politis, C. Tselios, P. Galiotos, and S. Kotsopoulos, “On Blockchain Enhanced Secure Network Coding for 5G Deployments,” in 2018 IEEE Global Communications Conference (GLOBECOM), 2018, pp. 1–7.
[13] A. Cohen, R. G. L. D’Oliveira, S. Salamatian, and M. Médard, “Network Coding-Based Post-Quantum Cryptography,” IEEE J. Sel. Areas Inf. Theory, vol. 2, no. 1, pp. 49–64, 2021.
Cite this article:
V. Adat (2021), Network Coding: A Multi-Faceted Enabler for Next-Generation Wireless Networks!, Insights2Techinfo, pp. 1-2
I am really impressed with your writing skill, it is rare to see a nice blog like this one nowadays..
Thank you!
Useful information. Lucky me I found your website accidentally, and I am shocked why this accident didn’t took place in advance! I bookmarked it.
Thank you
Its really impressive and informative. Great work.
Thank you