By: Nishita Verma, Department of CSE, Chandigarh College of Engineering and Technology, Panjab University, Chandigarh, Email- co24343@ccet.ac.in,
Abstract
6G technology, predicted to be fully adoptive by 2030, evolves to promise an excellent connectivity for IoT ecosystem but it raises a few security concerns. As the scale of 6G devices increases with Terahertz (THz) speeds, traditional security models fail to meet user requirements. This articles introduces advanced solutions for secure communication and access control, with a transformative integration of AI, blockchain, and post-quantum cryptography. A proposal of a native, zero-trust architecture instead of a perimeter-based algorithm is recognised, with the objective of achieving network integrity within the high speed, resource-constrained environments of 6G-IoT smart systems.
Keywords
6G Networks, IoT Security, Access Control, Zero-Trust Architecture, Blockchain, AI-Driven Security
Introduction
The Internet of Things (IoT), in terms of convenience of services, and the growth of incorporated devices, has been transformative. As 6G is expected for commercial deployment around 2030, the scale and speed of this connectivity is predicted to be 100 times faster than 5G. It set to grow exponentially in scale [3]. But, this relatively faster and successfully connectivity of around a million devices raises some concerns. When millions of devices engage in super-fast data communication, data privacy and network availability become a significant issue. Modern technologies, accumulated with 6G like Open Radio Access Networks (O-RAN) and Terahertz (THz) communication bands introduce new “attack surfaces” as opportunities for threats that traditional perimeter- based security approaches cannot remove [2]. This article opens up the “never trust, always verify” philosophy for evaluation to ensure network integrity in these complex smart systems [1].
Block diagram
The proposed architecture is comprising of three layers of abstraction and different security levels. The data flow goes from bottom to top, and the control flow goes from top to bottom:-
Application/Management Layer
The jurisdiction of this layer comes within smart cities and Industrial IoT. Security measures include Blockchain-based ledgers and Attribute-Based Access Control (ABAC) to manage user identities with great accuracy and no failure [14].
6G Communication & Edge Layer
This layer as a highly efficient filter. This layer utilises trustworthy Zero-Trust Verification and AI-Driven Intrusion Detection (IDS) to monitor data traffic in real-time [13].
Perception & Device Layer
Consists of resource-constrained IoT sensors and user wearables. Security here is controlled by Lightweight Cryptography and Physical Layer Security (PLS) to protect data at the source without draining battery life [6, 8].
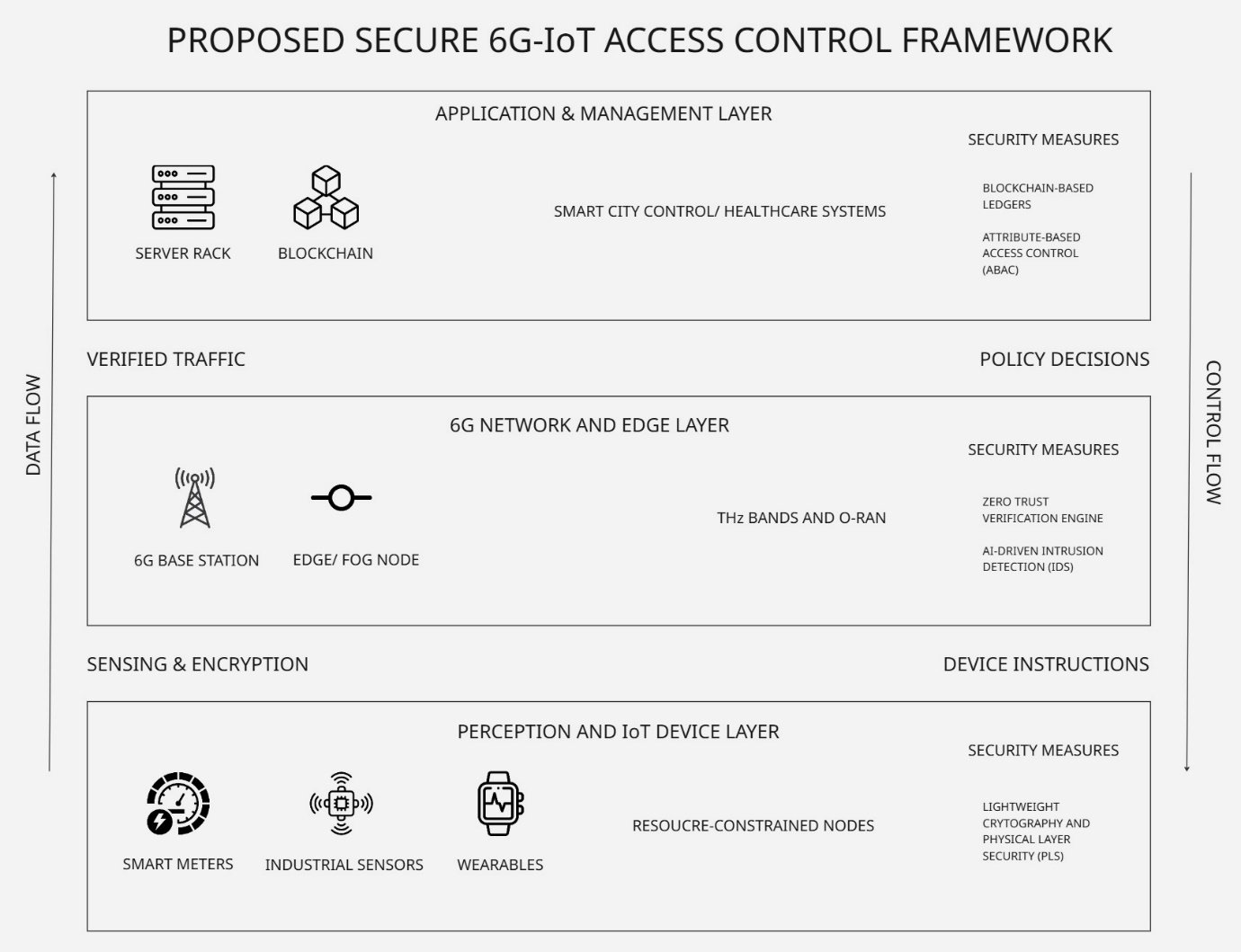 Fig 1: Proposed Secure 6G-IoT Access Control Framework
Fig 1: Proposed Secure 6G-IoT Access Control Framework
Methodology
6G-IoT leads to many vulnerabilities, so a carefully procured set of technologies is needed for it to work and be secure in communication and seamless connectivity:
- Secure Communication: Utilisation of the many algorithms of Post-Quantum Cryptography (PQC) is done to defend against future quantum computer attacks that could break standard RSA/ECC encryption [6]. Furthermore, PLS exploits the physical properties of the radio signal in THz bands to prevent eavesdropping, so any foreign user trying to listen to a secure communication will only hear white noise [8].
- Identity & Access Management: In a solid transition from perimeter-based security protocols, a zero-trust system is suitable. Every request is continuously authenticated, even if the node communicating has been in the network for a while. Blockchain technology eliminates the single point of failure in centralized systems using this architecture [7, 8].
- Artificial Intelligence: Implementing fine-tuned Convolutional Neural Networks (CNNs) at the network edge allows for an accurate malware detection and anomaly removal before threats reach the core network [11, 13]. This is an active approach of removing threats by integrating AI within our security system.
Experiment and Expected result
Studies from 20205 for AI-driven models provides a relieving conclusion for the risk of concerns that are not covered by our primary defences. By using hardware-supported parallelization architectures [14], 6G systems can regulate massive data throughput without the speculative overheads, which wasn’t possible in the previous generation of networks. Simulations of these models for 6G-IoT networks have demonstrated a 97% to 99.9% detection accuracy for emerging cyber threats, hence ensuring an active security system [10, 11]. Moreover, applying Federated Learning-based models ensures that while the system learns to identify attacks using data, the raw data remains decentralized, significantly enhancing user privacy in critical infrastructure [12]. This addresses our concern of data privacy, and hence, more users can actively adopt this technology in the future.
Conclusion
Secure communication and access control are the integral components for the success of smart cities and connected healthcare. The transition from 5G to 6G requires security to be “native” built into the protocols and hardware initially, not just as an additional attractive feature. While more challenges like device heterogeneity and the resource constraints of IoT still remain, the convergence of PQC, AI, Blockchain, and Zero-Trust architectures provides a successful outlook on this approach. Balancing the speed of 6G with the safety of these intelligent frameworks is essential for the next two decades of global connectivity and seamless and secure communication.
References
- C. Romero and S. Ventura, “A survey on the security challenges of IoT-enabled next-generation networks,” IEEE Trans. Netw. Serv. Manag., vol. 18, no. 3, 2021.
- N. Kaur and L. Gupta, “Securing the 6G-IoT Environment: A Framework for Enhancing Transparency,” Sensors, vol. 25, no. 3, 2025.
- F. Tariq et al., “A Speculative Study on 6G,” IEEE Wireless Commun., vol. 27, no. 4, 2020.
- A. M. Alwakeel and A. K. Alnaim, “Network Slicing in 6G for IoT in Smart Cities,” Sensors, vol. 24, no. 13, 2024.
- A. Pardo and G. Siemens, “Ethical and privacy principles for learning analytics,” Br. J. Educ. Technol., vol. 45, no. 3, 2014.
- Y. Mao et al., “Security Requirements and Challenges of 6G Technologies,” PMC / MDPI, 2022.
- M. Frustaci et al., “Access Control for IoT: A Survey,” PMC, 2023.
- S. Nie et al., “Zero-Trust Access Control Mechanism Based on Blockchain in 6G,” Sensors, vol. 25, no. 2, 2025.
- H. Al-Hmood and H. S. Al-Raweshidy, “A Physical Layer Security Scheme for 6G,” J. Ind. Inf. Integr., 2024.
- M. Liyanage et al., “Zero-Trust Mechanisms for Edge and Fog Computing in 6G,” Mathematics, vol. 13, no. 8, 2025.
- S. Kumar and S. K. Singh, “MCFT-CNN: Malware classification with fine-tune convolution neural networks in Internet of Things,” Future Generation Computer Systems, vol. 122, 2021.
- A. Sharma, S. K. Singh, and S. Kumar, “A Novel Deep Federated Learning-Based Model to Enhance Privacy in Critical Infrastructure Systems,” IJSSCI, 2023.
- R. Singh, S. K. Singh, and S. Kumar, “SDN-Aided Edge Computing-Enabled AI for IoT and Smart Cities,” SDN-Supported Edge-Cloud Interplay, 2022.
- S. Kumar, S. K. Singh, and B. B. Gupta, “An efficient hardware supported and parallelization architecture for intelligent systems to overcome speculative overheads,” International Journal of Intelligent Systems, vol. 37, no. 12, 2022.
- Zhou, Z., Gaurav, A., Gupta, B. B., Lytras, M. D., & Razzak, I. (2021). A fine-grained access control and security approach for intelligent vehicular transport in 6G communication system. IEEE transactions on intelligent transportation systems, 23(7), 9726-9735.
- Gaurav, A., Gupta, B. B., & Panigrahi, P. K. (2023). A comprehensive survey on machine learning approaches for malware detection in IoT-based enterprise information system. Enterprise Information Systems, 17(3), 2023764.
Cite As
Verma N. (2026) Secure Communication and Access Control in IoT-Enabled 6G Smart Systems, Insights2Techinfo, pp.1