By: Piyush, Department of Computer Science & Engineering, CCET (Degree wing), Chandigarh, India, Email: Co24345@ccet.ac.in
Abstract
The cybersecurity environment in 2026 is not about prevention anymore; rather, it is all about early detection and quick recovery, whatever happens. In the meantime, AI has affected both the attacker’s and defender’s side. The WEF’s report “Global Cybersecurity Outlook 2026” says that 94% of those who participated think that AI will be the most influential trend impacting cybersecurity in the coming years, whereas 87% consider AI-related cybersecurity threats to have the highest growth rates[6]. This article analyzes the current state of affairs: autonomous cyber-attacks, Zero Trust authentication, federated learning for edge environments, adversarial model attacks, and regulatory compliance requirements for organizations. The goal is a practical picture of what’s working and where the gaps still are(3).
Keywords
Artificial Intelligence, Cybersecurity, Zero Trust Architecture, Federated Learning, IoT Security, Smart Cities, Post-Quantum Cryptography, Adversarial Machine Learning, Autonomous SOC, AI Governance
Introduction
The smart city industry surpassed the $952 billion mark in 2025 and is projected to grow further to reach a $6.3 trillion market value in 2034[10]. There is no way the sheer magnitude of infrastructure can be monitored without AI and IoT, there is no alternative. Yet, this reliance on AI and IoT poses its own challenge – the more connected a city or an enterprise is, the more attack vectors will emerge. Ten years ago, cybersecurity relied on solid perimeter defences. This paradigm has been thoroughly debunked since. Threat actors now operate via third-party integrations, misconfigured sensors, and supply chain attacks, often outpacing human monitoring teams’ efforts[8]. Simultaneously, defenders deploy AI systems to automate their monitoring tasks, mitigate vulnerabilities before they are used, and deal with millions of machine identities that are not accounted for by legacy technologies. This article seeks to map the trends around these challenges in six categories: offensive AI, autonomous defence, Zero Trust and identity, smart cities and IoT security, edge AI and federated learning, and adversarial robustness. The methodology, expected experimental outcomes, and governance implications are discussed in turn.
Block Diagram
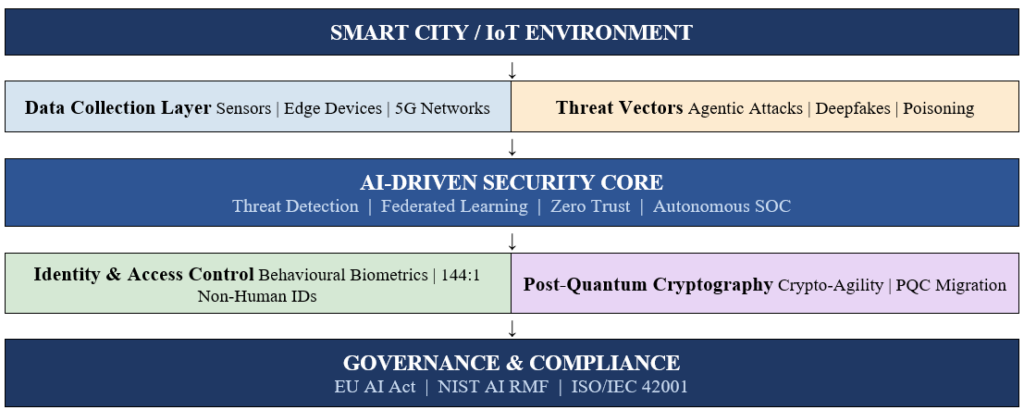
Figure 1 below shows how the major components of AI-driven cybersecurity interact in a smart and connected environment from the physical IoT layer through threat detection, identity control, and regulatory governance.
Methodology
The present article is based on an analysis of industrial sources, academic publications, and practical examples available from 2021 through 2026. In selecting sources, particular attention was paid to their connection with AI-based approaches to security in the context of smart cities and IoT technologies, with an emphasis on empirical findings rather than theoretical approaches. From a technical perspective, the central security model that will be considered in the study is Federated Learning (FL), which can train models using only distributed devices’ edge nodes without transferring data to other machines (1). Frameworks like Edge-FLGuard pair autoencoder and LSTM networks for anomaly detection directly on 5G-connected edge hardware, achieving F1-scores above 0.91 and inference latency under 20 milliseconds(7). Model compression is a necessary companion: knowledge distillation keeps accuracy at 94% of the full model even at 4-bit quantisation, versus a 70% drop without it (1). The Zero Trust component is evaluated through its impact on identity management, particularly the challenge of securing the estimated 144 non-human identities per human user now present in enterprise environments, a figure growing at 44% per year(8). Behavioural biometrics typing cadence, cursor movement, touch pressure are assessed as passive continuous verification tools that reduce friction while raising the bar for credential-based attacks(3). Adversarial robustness is evaluated against two threat classes: data poisoning (label-flipping attacks causing up to 40% accuracy drops) and prompt injection against LLMs, both of which require active countermeasures rather than passive monitoring (11). Finally, governance readiness is mapped against three frameworks: the EU AI Act, NIST AI RMF, and ISO/IEC 42001, which differ primarily in whether compliance is mandatory, certifiable, or advisory(2)(4).
Experiment and Expected Results
The proposed framework combines FL-based edge intrusion detection with Zero Trust identity verification and AI-driven SOC automation. To validate it, the experimental design targets three measurable outcomes. First, detection performance: deploying the Edge-FLGuard architecture on a simulated 5G-IoT testbed with 100 client nodes, with an expected F1-score of 0.91 or higher and sustained detection latency below 20ms even under 40% client compromise(7). Second, breach lifecycle optimization: incorporating AI-powered XDR and next generation SIEM within the SOC, focusing on the reported decrease in breach lifecycle by 80 days and the saving of $1.9 million per breach event when contrasted with manual remediation(10). Third, Identity resilience: applying real-time behavioral biometric authentication across human and machine identities, achieving a 76 percent decrease in successful breaches(8).
The findings from actual implementations in comparable situations validate these estimates. The AI-based streetlights installed in Berlin reduced power consumption by 40 percent. The incorporation of Internet of Things alerts and predictive analysis within the Smart Nation project of Singapore helped reduce downtime. Hamburg’s digital twin simulations allowed administrators to test cyberattack scenarios on port logistics before incidents occurred(5)(9). Maintenance cost savings of 25-30% and emergency response improvements of 40-50% are documented across similar smart infrastructure programmes(10). On the adversarial front, organisations using adversarial training and Explainable AI (XAI) pipelines have demonstrably outperformed those relying on static detection rules particularly against poisoning attacks that would otherwise degrade classifier accuracy from 95% to around 60%(11). Post-quantum cryptography migration, using crypto-agile architectures that allow algorithm swaps without system rebuilds, is expected to become a compliance requirement in finance and defence within the next two to three years(12).
Taken together, these projected outcomes suggest that an integrated AI security stack FL at the edge, Zero Trust at the identity layer, autonomous response at the SOC, and XAI for model integrity produces significantly better outcomes than any single component deployed in isolation. The governance layer, particularly alignment with the EU AI Act’s mandatory requirements for high-risk systems in critical infrastructure, provides the accountability structure that makes these results sustainable(4)(5).
Conclusion
From the perspective of 2026, the general trend is clearly towards escalating capabilities for both sides. Attackers can act autonomously, adapt in real-time, and scale up in a manner which is impossible to counter by human-operated security operations(6). Organisations who perform better on this front have moved away from static defences toward proactive, AI-based monitoring using identity as the main control plane, with detection being done at the edges rather than in a centralised fashion, and with governance procedures capable of tracking automated decision-making processes(1)(2). Adversarial ML attacks against the defensive algorithms, which may quietly affect their effectiveness without producing an alarm, and the transition to a post-quantum world where attacks will be technically possible despite the fact that they’re still far from reality – two topics which warrant much more attention than currently paid to them. The proposed approach – federated learning, Zero Trust identity management, autonomous SOC, and explainable AI – may not constitute the full solution, but provides a solid blueprint for investments to be made.
References
- Sharma, A., Singh, S.K., Chhabra, A., Kumar, S., Arya, V. and Moslehpour, M. (2023). A Novel Deep Federated Learning-Based Model to Enhance Privacy in Critical Infrastructure Systems. International Journal of Software Science and Computational Intelligence, 15(1), 1–23. DOI: 10.4018/IJSSCI.334711
- Mengi, G., Singh, S.K., Kumar, S., Mahto, D. and Sharma, A. (2022). Automated Machine Learning (AutoML): The Future of Computational Intelligence. In ICSPN 2022, pp. 309–317. Springer. DOI: 10.1007/978-3-031-22018-0_28
- Kumar, S., Karnani, G., Gaur, M.S. and Mishra, A. (2021). Cloud Security using Hybrid Cryptography Algorithms. In ICIEM 2021, pp. 599–604. IEEE. DOI: 10.1109/ICIEM51511.2021.9445377
- Thakur, U., Singh, S.K., Kumar, S., Singh, H., Arya, V. and Gupta, B.B. (2025). Advanced Web Traffic Modelling and Forecasting with a Hybrid Predictive Approach. Journal of Web Engineering, 24(03), 409–456. DOI: 10.13052/jwe1540-9589.2434
- Peñalvo, F.J.G., Sharma, A., Chhabra, A., Singh, S.K., Kumar, S. and Arya, V. (2022). Mobile Cloud Computing and Sustainable Development: Opportunities, Challenges, and Future Directions. International Journal of Cloud Applications and Computing, 12(1), 1–20. DOI: 10.4018/IJCAC.312583
- World Economic Forum. (2026). Global Cybersecurity Outlook 2026. WEF Annual Report. Available at: https://reports.weforum.org
- MDPI. (2026). Edge-FLGuard: A Federated Learning Framework for Real-Time Anomaly Detection in 5G-enabled IoT. Available at: https://mdpi.com
- NetWitness. (2026). SIEM’s Role in Zero Trust Architecture in 2026 and Beyond. Available at: https://netwitness.com
- DigitalDefynd. (2026). AI in Smart Cities: 8 Case Studies 2026. Available at: https://digitaldefynd.com
- iFactory Application Solutions. (2026). AI and IoT in Smart City Infrastructure: 2025 Global Trends Report. Available at: https://ifactoryapp.com
- arXiv. (2026). Robustness Analysis of Machine Learning Models for IoT Intrusion Detection Under Data Poisoning Attacks. Available at: https://arxiv.org
- EC-Council University. (2026). Top Cybersecurity Trends of 2026: AI, Zero Trust and Quantum Security. Available at: https://eccu.edu
- Ho, G. T. S., Tang, Y. M., Kuo, W. T., & Tang, V. (2025), “Blockchain‐Based Platform for Information Security and Visual Management in Coffee Trading”, Concurrency and Computation: Practice and Experience, 37(25-26), e70299.
- Bhushan, K., & Gupta, B. B. (2017). Security challenges in cloud computing: state-of-art. International Journal of Big Data Intelligence, 4(2), 81-107.
- Gupta, S., & Gupta, B. B. (2017). Detection, avoidance, and attack pattern mechanisms in modern web application vulnerabilities: present and future challenges. International Journal of Cloud Applications and Computing (IJCAC), 7(3), 1-43.
Cite As
Piyus (2026) Emerging Trends in AI-Driven Cybersecurity for Smart and Connected Environments, Insights2Techinfo, pp.1