By: Sneha, Department of Computer Science & Engineering, Chandigarh College of Engineering and Technology, Chandigarh (160019), India, Email: sneha727577@gmail.com
Abstract
Outside a few data centers, there is a distributed computer system running over clouds, near-user gadgets, and networked systems that make it easier for hackers. A dispersed control system means that all kinds of tricks come through, like fake login screens in addition to ransomware, traffic floods that crash systems, invisible malware, and listening devices that copy information while it’s still being sent. With many different ways in to the system, security can be hard to keep consistent and is under constant development to defend against new threats. When they go through a way that security was broken, tools to detect intruders become a very common topic in these discussions, as well as some security tools that can be used to build defenses like encryption and multi-factor authentication.
Keywords
Cyber Security, Distributed Systems, IDS, DDoS, Phishing, IoT Security
I. Introduction
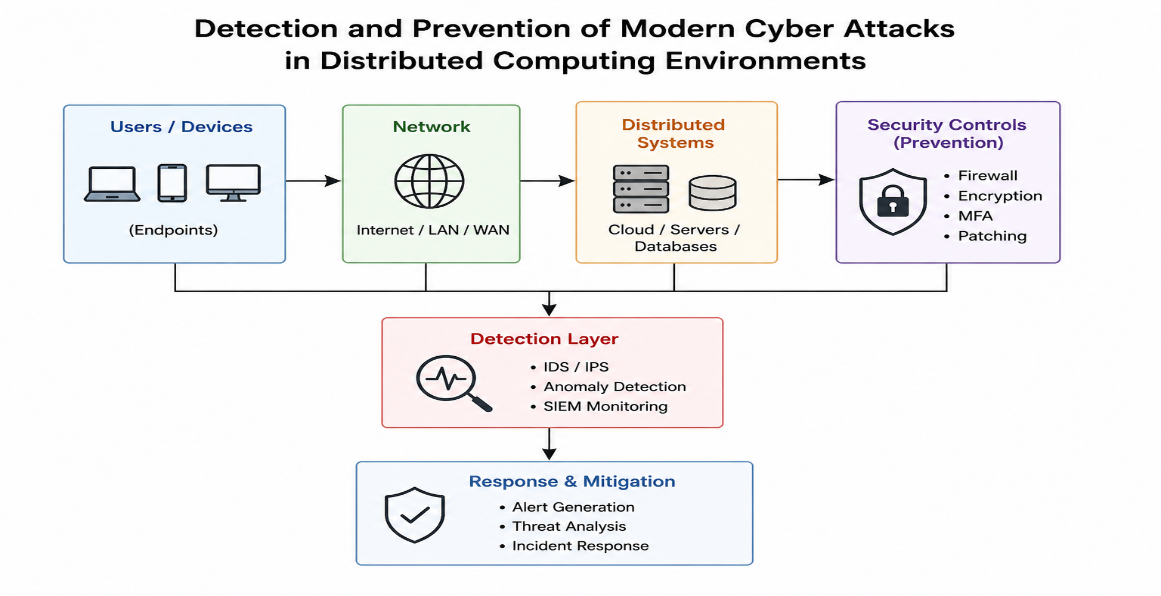
There are a variety of computers that work together across networks to form services with applications and databases running on them in order to keep systems responsive, accessible and scalable. This applies to smart devices, enterprise systems and services running on remote machines. However, it is not just on the outside boundary that protection must be afforded to systems; each component, both hardware and software along with all of the communications infrastructure, must be self-protecting [11]. As data moves relentlessly between machines; any weakness at any component may have an impact across the whole service, meaning that security has become paramount. Fig 1 give a pictorial overview of detection and prevention of modern cyber attacks in distributed computing environment[10].
III. Methodology
The overall concept relies on threat identification followed by layering security defenses.
Phishing, Ransomware, DDoS, Malware, MITM are few types of present cyber attacks. Phishing involves stealing the authentication using social engineering techniques [3]. Ransomware involves encrypting files then demanding a ransom. DDoS attacks utilize large amount of data over-load and malware is any type of software causing disturbance over a network.
Intrusion Detection systems (IDS) helps in detecting these types of threats and monitor the network and the system [6][7][8]. There are signature and anomaly based detection systems[4]. Machine learning techniques have an added advantage for identifying abnormal patterns [1][2][9]. SIEM tools combine logs from various sources [5].
IV. Experiment and Expected Result
This system helps monitor network activity and detect unusual activity in a distributed setting. If abnormal activity like anomalous login attempt or unusual network traffic is detected, IDS will trigger an alarm. ML will help classify the activity as malicious or normal.
Expected outcome:
- Cyber-attacks are detected more quickly.
- System downtime is reduced.
- Security of distributed system is increased.
- Anomalous activity is detected more accurately.
V. Conclusion
Even though distributed systems scale so well, they have very high security vulnerabilities. The flaw that is present in a distributed system that is exploiting by attackers using attacks such as phishing, ransomware and maleware is widespread. To defend these types of attacks, security must be handled in layers, encompassing features such as logging, encryption and authentication. Security is not a process of one time event, but on ongoing process.
References
- Kumar, S., Singh, S. K., Kumar, R., Subba, C. K., Chui, K. T., & Gupta, B. B. (2025). Neoteric threat intelligence ensuring digital sovereignty and trust through ML-infused proactive defense analytics for NEXT-G and beyond ecosystems. Procedia Computer Science, 254, 39-47.
- Vashisht, H., Singh, S. K., Kumar, S., Singh, N., Arya, V., Chui, K. T., & Gupta, B. B. (2026, February). IoT-XPLAIN: Intelligent Fault Detection and Natural Language Explanation for IoT Systems Using ML and LLMs. In 2026 28th International Conference on Advanced Communications Technology (ICACT) (pp. 1-6). IEEE.
- Muku, A., Singh, S. K., Kumar, S., Sharma, A., Rai, P., Upadhyaya, B., … & Sharma, V. (2025). Phishing prevention solutions and mechanisms. In Critical Phishing Defense Strategies and Digital Asset Protection (pp. 49-72). IGI Global Scientific Publishing.
- Jaggi, S., Singh, S. K., Kumar, S., Arora, R., Bansal, S., & Arya, V. (2026). Approaches for misuse and anomaly detection in IoT ecosystems. In Internet of Things Security (pp. 107-127). Elsevier.
- Arora, S., Kumar, S., Singh, S. K., Garg, S., & Gupta, B. B. (2026). Microservice architecture for securing distributed IoT. In Internet of Things Security (pp. 175-199). Elsevier.
- Gupta, N., Jindal, V., & Bedi, P. (2023). A survey on intrusion detection and prevention systems. SN Computer Science, 4(5), 439.
- Abdulganiyu, O. H., Ait Tchakoucht, T., & Saheed, Y. K. (2023). A systematic literature review for network intrusion detection system (IDS). International journal of information security, 22(5), 1125-1162.
- Sen, J. (2010, October). A robust and fault-tolerant distributed intrusion detection system. In 2010 First International Conference On Parallel, Distributed and Grid Computing (PDGC 2010) (pp. 123-128). IEEE.
- Han, P., Li, H., Xue, G., & Zhang, C. (2023). Distributed system anomaly detection using deep learning‐based log analysis. Computational Intelligence, 39(3), 433-455.
- Modi, C., Patel, D., Borisaniya, B., Patel, H., Patel, A., & Rajarajan, M. (2013). A survey of intrusion detection techniques in cloud. Journal of network and computer applications, 36(1), 42-57.
- Rose, S., Borchert, O., Mitchell, S., & Connelly, S. (2020). Zero trust architecture. NIST special publication, 800(207), 1-52.
- Bhushan, K., & Gupta, B. B. (2017). Security challenges in cloud computing: state-of-art. International Journal of Big Data Intelligence, 4(2), 81-107.
- Ho, G. T. S., Tang, Y. M., Kuo, W. T., & Tang, V. (2025), “Blockchain‐Based Platform for Information Security and Visual Management in Coffee Trading”, Concurrency and Computation: Practice and Experience, 37(25-26), e70299.
Cite As
Sneha (2026), Detection and Prevention of Modern Cyber Attacks in Distributed Computing Environments, Insights2Techinfo, pp.1