By: Devesh Vaidya, Chandigarh College of Engineering and Technology, Panjab University, Chandigarh, India, Email: co24317@ccet.ac.in
Abstract
The concept of data-driven cybersecurity frameworks involves the use of big data analytics, artificial intelligence, and new-age security methodologies to protect smart enterprise environments. With more and more firms turning to cloud computing, Internet of Things (IoT), and digital transformation, traditional security tools have become insufficient to deal with sophisticated and ever-changing cyber threats. Through the deployment of big data analytics, machine learning models, and real-time monitoring systems, these frameworks ensure better threat detection, improved risk assessments, and automated responses. The current paper will discuss the basic features of data-driven cybersecurity, the technologies used in them, applications, advantages, disadvantages, and future prospects.
Key words : Big Data Analytics , Machine Learning , Intrusion Detection Systems (IDS) , Security Information and Event Management (SIEM) , Cyber-Physical Systems Security , Predictive Threat Intelligence
Introduction
Advancements in digital technology have resulted in the creation of extremely connected enterprise systems that incorporate cloud technology, Internet of Things (IoT), and industrial automation systems. Although such innovations efficiency and scalability in enterprises, they create new risks for cybersecurity. Conventional cybersecurity solutions based on rules and signatures are not sufficient in detecting and countering increasingly complex and evolving cyber-attacks. Data-driven cybersecurity involves collecting vast amounts of data, conducting deep analysis, and using artificial intelligence to detect, predict, and counteract cybersecurity risks [1]. Contrary to conventional cybersecurity solutions, data-driven cybersecurity technologies continuously learn from historical and real-time data, allowing firms to deploy preemptive cybersecurity policies. This paper highlights the benefits of data-driven cybersecurity in smart enterprise systems, its associated technologies, and wider implications across different industries.
Data-Driven Cybersecurity Technologies
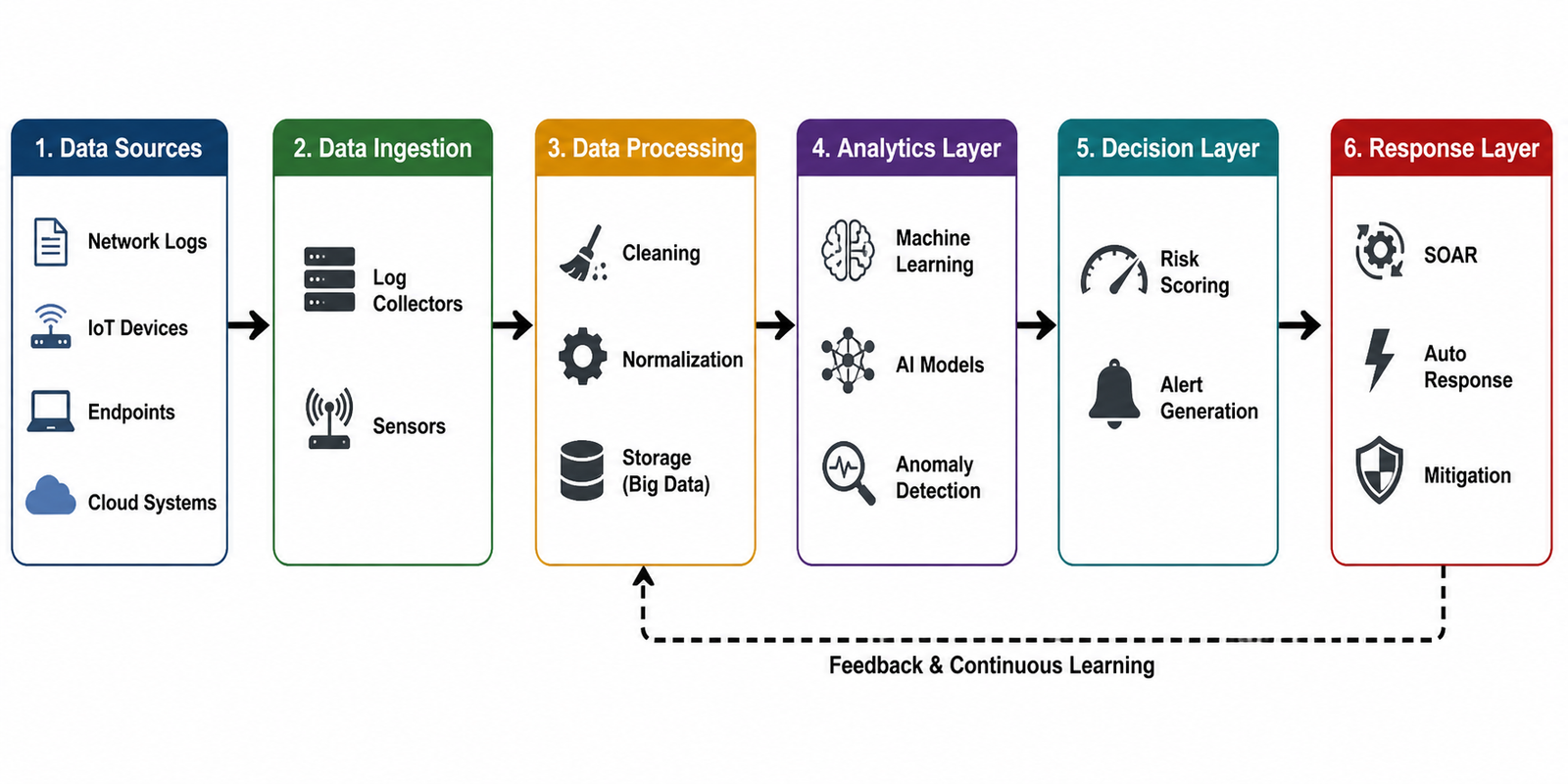
Cybersecurity systems based on data processing use an integrated technical system created to ensure intelligent detection and protection against cyber threats. A basic element of the technology stack used is the analysis of large data sets containing structured and unstructured data obtained from various sources such as logs, IoT devices, endpoints, and cloud services. [2] The acquisition process uses scalable methods for data collection and storage in distributed systems, where data are preprocessed and normalized. Artificial intelligence and machine learning technologies help to extract information from data by detecting regularities, analyzing deviations, and improving algorithms’ performance by self-learning. In addition, Security Information and Event Management systems provide centralized monitoring by collecting and analyzing security-related events. Security Orchestration, Automation, and Response platforms automate detection and response operations to reduce response time and increase efficiency. Cloud and edge computing security systems help manage the data obtained from distributed sources and analyze data in real-time. This technology set helps move cybersecurity management from reactive approaches to predicting and preventing attacks..
The Role of Data-Driven Cybersecurity in Smart Enterprises
Data-driven cyber security proves to be highly effective for mitigating cyber threats in intelligent enterprises due to the following reasons. The combination of information technology and OT/IoT technologies increases interconnectivity of systems. As a result, there is an increase in the number of opportunities through which the company’s system can be attacked. Data-driven cyber security can overcome this problem because it allows for continuous monitoring and analysis of what is happening within the network. [3] A number of advanced techniques and methods used in data-driven cyber security enable the detection of anomalies that could indicate a future threat. This process becomes even more efficient due to machine learning that identifies new threats, while conventional methods lack this ability. Moreover, data-driven cyber security makes it possible to predict cyber attacks as well as to determine what vulnerabilities can lead to such attacks and estimate their probability to develop preventive actions. This approach has broad applicability to various types of businesses, including healthcare systems that store sensitive patient information and use connected medical devices, finance companies, industrial enterprises, especially those engaged in smart manufacturing.
Cyber Threat Detection and Response Lifecycle
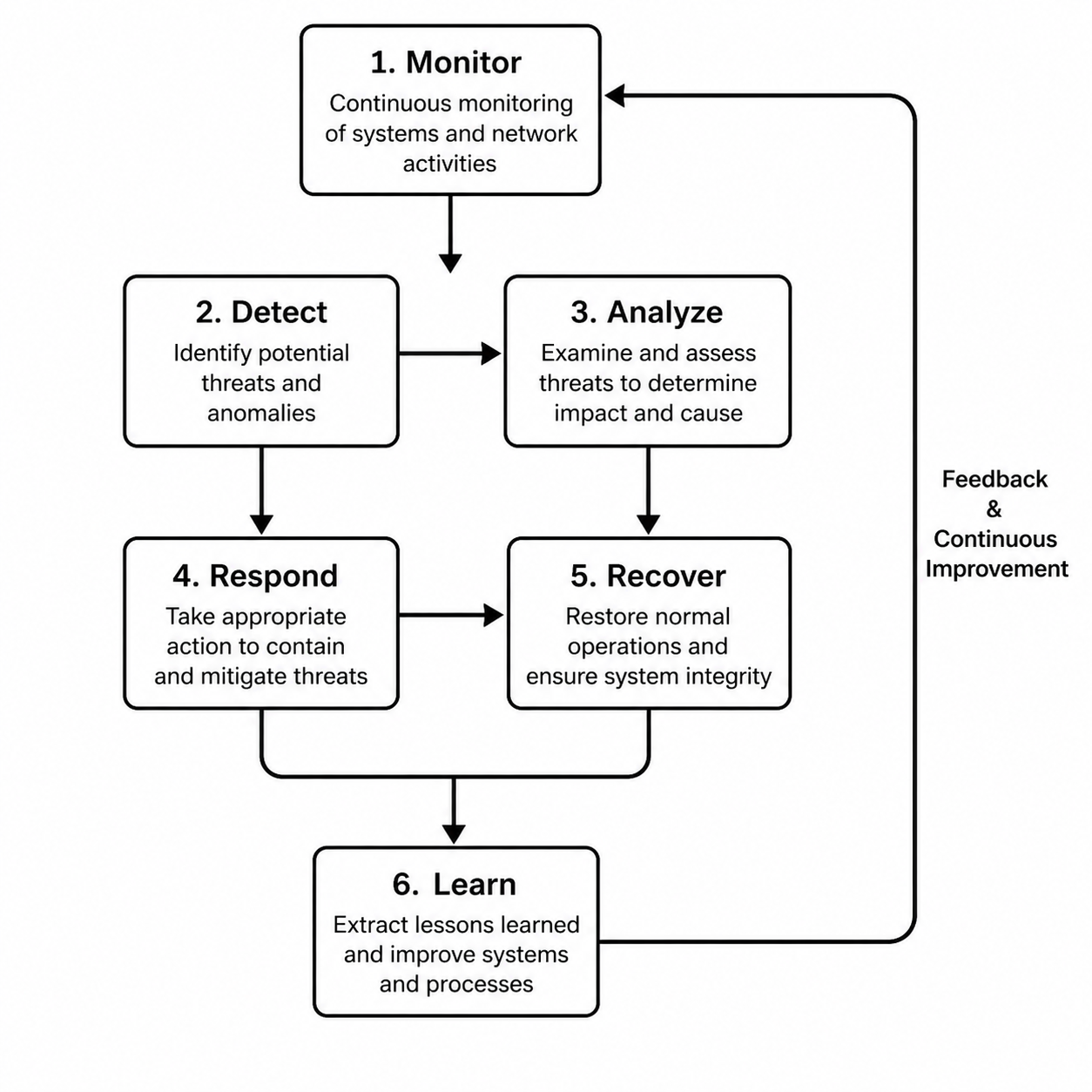
One crucial aspect of data-driven cybersecurity is the continuous loop between threat detection and response, which provides continuous protection for enterprise systems. First, there is constant surveillance, whereby information is continuously collected from various parts of the enterprise systems. Then, through analysis with the help of machine learning, the nature of any anomaly or possible breach is determined.[4] Once the nature of the threat has been identified, an action plan is put in place to deal with the threat. If necessary, the system will automatically isolate any compromised part of the enterprise systems or block any malicious activity.Once the issue has been sorted out, the system undertakes recovery processes to bring back operations to normalcy. The most significant thing about this cycle is that there is a continuous feedback system within it. Through this feedback system, any lessons learnt are used to enhance the system in the future.
Machine Learning-Based Intrusion Detection System
Machine learning-enabled intrusion detection systems [5] represent a vital part of today’s cybersecurity solutions. These systems operate by examining vast amounts of network traffic and system logs for any signs of suspicious activity. Initially, a data collection phase is carried out, which is followed by feature extraction, when particular attributes, such as traffic flow or protocols employed, are singled out. This information is used to train machine learning algorithms that are able to differentiate between normal and abnormal system behavior. The trained model can then evaluate incoming information in real-time and classify it appropriately. Any signs of a threat trigger alerts and take corrective measures. Machine learning-enabled intrusion detection systems outperform conventional systems in terms of efficiency and accuracy. [6]
Challenges and Limitations
Although data-driven approaches have many benefits, there are some difficulties that limit their implementation on a wider scale. First, one has to address the problems associated with the management of enormous volumes of different data provided by various enterprise systems. Moreover, real-time data analysis imposes certain restrictions related to the necessity for high-performance computing capacities[7]. In terms of methods, machine learning algorithms might not always ensure accuracy and lead to incorrect predictions of malicious actions. Another challenge relates to the complex nature of machine learning algorithms, which makes them hard to explain to users. [8] Financial aspects should also be considered because the application of modern cybersecurity solutions necessitates substantial financial and professional investments. Moreover, privacy-related problems may emerge due to the analysis of user data.[9]
Conclusion
Data-driven cybersecurity systems are among the notable achievements in securing modern enterprises due to their intelligent, proactive, and responsive nature. With the incorporation of big data analysis, artificial intelligence, and automated responses to potential cyberattacks, such systems have proved to be more efficient in threat detection and mitigation. Challenges associated with data analysis, cost issues, and ethics, however, need to be sorted out in order for this type of cybersecurity to succeed. [10]As technology advances, it is predicted that data-driven cybersecurity will play a key role in making future enterprise systems smart and resilient to cyber threats.
References
- A. Sharma, S. K. Singh, S. Kumar, A. Chhabra, and S. Gupta, “Security of Android Banking Mobile Apps: Challenges and Opportunities,” in International Conference on Cyber Security, Privacy and Networking (ICSPN 2022), vol. 599, N. Nedjah, G. Martínez Pérez, and B. B. Gupta, Eds., in Lecture Notes in Networks and Systems, vol. 599. , Cham: Springer International Publishing, 2023, pp. 406–416. doi: 10.1007/978-3-031-22018-0_39.
- H. Gupta et al., “Variance‐driven security optimisation in industrial IoT sensors,” IET Netw., vol. 14, no. 1, p. e12139, Jan. 2025, doi: 10.1049/ntw2.12139.
- A. Sharma, S. K. Singh, S. Kumar, R. Thakur, B. B. Gupta, and V. Arya, “IoT-enabled smart farming with Industry 5.0,” J. High Speed Netw., vol. 30, no. 3, pp. 477–496, Aug. 2024, doi: 10.3233/JHS-230258.
- V. Singla et al., “Challenges and Opportunities in Sustainable AI and Information Systems:,” in Advances in Computational Intelligence and Robotics, B. B. Gupta, D. Pramod, and M. Moslehpour, Eds., IGI Global Scientific Publishing, 2025, pp. 73–96. doi: 10.4018/979-8-3693-8034-5.ch004.
- I. Singh, S. K. Singh, R. Singh, and S. Kumar, “Efficient Loop Unrolling Factor Prediction Algorithm using Machine Learning Models,” in 2022 3rd International Conference for Emerging Technology (INCET), Belgaum, India: IEEE, May 2022, pp. 1–8. doi: 10.1109/INCET54531.2022.9825092.
- F. J. G. Peñalvo et al., “Sustainable Stock Market Prediction Framework Using Machine Learning Models:,” Int. J. Softw. Sci. Comput. Intell., vol. 14, no. 1, pp. 1–15, Nov. 2022, doi: 10.4018/IJSSCI.313593.
- R. Kumar, S. K. Singh, D. K. Lobiyal, and S. Kumar, “Secure and cost-effective key management scheme for the Internet of Things-supported WSN,” in Uncertainty in Computational Intelligence-Based Decision Making, Elsevier, 2025, pp. 277–292. doi: 10.1016/B978-0-443-21475-2.00012-6.
- C. Tankard, “Advanced Persistent threats and how to monitor and deter them,” Netw. Secur., vol. 2011, no. 8, pp. 16–19, Aug. 2011, doi: 10.1016/S1353-4858(11)70086-1.
- T. Singh et al., “Enhancing Autonomous System Security With AI and Secure Computation Technologies:,” in Advances in Computational Intelligence and Robotics, B. B. Gupta and F. Colace, Eds., IGI Global, 2025, pp. 159–186. doi: 10.4018/979-8-3693-2707-4.ch008.
- R. Kumar, S. K. Singh, D. K. Lobiyal, S. Kumar, and S. Jawla, “Security Metrics and Authentication-based RouTing (SMART) Protocol for Vehicular IoT Networks,” SN Comput. Sci., vol. 5, no. 2, p. 236, Jan. 2024, doi: 10.1007/s42979-023-02566-7.
- Gaurav, A., Gupta, B. B., & Panigrahi, P. K. (2023). A comprehensive survey on machine learning approaches for malware detection in IoT-based enterprise information system. Enterprise Information Systems, 17(3), 2023764.
- Bhushan, K., & Gupta, B. B. (2017). Security challenges in cloud computing: state-of-art. International Journal of Big Data Intelligence, 4(2), 81-107.
Cite As
Devesh V. (2026) Data-Driven Cybersecurity Framework for Smart Enterprise Systems, Insights2Techinfo, pp.1