By: KUKUTLA TEJONATH REDDY, International Center for AI and Cyber Security Research and Innovations (CCRI), Asia University, Taiwan, tejonath45@gmail.com
Abstract:
Since smartphones play a major role in our daily lives, mobile phishing is become more common. In order to put more understanding of the strategies used by hackers, this article examines the topic of mobile phishing and breaks down its definition. Gaining the knowledge users need to recognize and prevent these fraudulent approaches is the main goal. We expose common techniques used by cybercriminals, that include social engineering and fake applications to SMS phishing. It highlights the importance of carefully examining the sender’s legitimacy, pausing before clicking, and using security software. The article offers an in-depth how to identify mobile phishing. Users can navigate the online environment with enhanced security and resilience against mobile phishing threats by understanding these strategies and implementing preventive measures.
Introduction:
In the quickly evolving world of technology, mobile devices play a crucial role in our everyday existence. This growing trust increases the risk of mobile phishing, fraudulent access to private information including bank account details, login passwords and personal information [1]. The following article will go into mobile phishing definitions, techniques commonly used by attackers and the most important as they are formidable and protect against falling for such frauds to be performed [2].
Understanding Mobile Phishing:
Mobile Phishing is a type of cyber-attack that targets people using their smartphones or mobile devices. The main goal is to persuade users to disclose confidentiality as a trustworthy company. Attackers often use a variety of techniques to create a false sense of legitimacy, making it difficult for users to distinguish a connection from a transaction between truth and illusion [3].
Common Mobile Phishing Tactics:
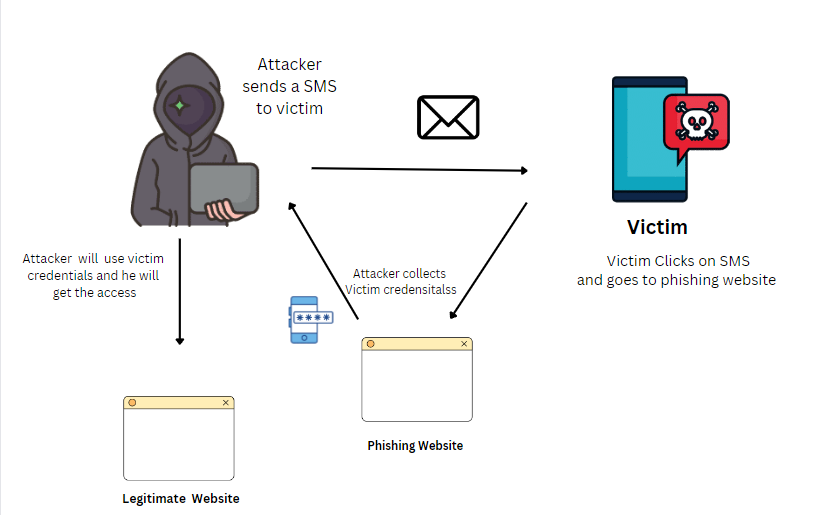
SMS Phishing (Smishing):
SMS phishing, also known as “smishing,” is a sneaky way for cybercriminals to use text messages in an attempt to trick people. They send messages that appear to be from trustworthy organizations, such banks or other organizations you use; these messages could have phone numbers or links in them. The intention is to deceive you into clicking on those links or disclosing sensitive information, such credit card numbers or passwords. Take attention and never click on anything in a text message unless you are confident it is coming from a trustworthy source in order to secure your information [5].
Email Phishing:
Attackers send phishing emails from trusted and genuine sources such as banks or online companies. These emails may ask you to reveal sensitive information such as your password or credit card information, or click on links that appear to do such work but are actually harming So Email seems to be a capable source reliable, but not [6]. So, be careful and avoid clicking on any links or entering any personal information in an email unless you are confident that it is coming from an authentic and reliable source. This is one way you can maintain the privacy of your data.
Fake apps:
Fake apps which appear to be original mobile application created by hacker through the network. Some of these apps are even everyday ones like the app for shopping and playing. However, the problem is that these rogue apps are developed with an objective of being installed on a phone where they pilfer your financial account details like, credit cards numbers or password. This is how they cheat me to feel like I am still using the real app but, in reality, I got another bad one. This is an awkward method of breaching into your personal info. It is necessary to download only these applications from trustworthy resources, for instance, the official online shop.
How to Detect Mobile Phishing:
Check the Sender’s Authenticity:
Look at the details of the sender’s email address or phone number and make sure they are genuine. Watch out for little spelling errors, minor changes in words which may be a sign of phishing [6].
Think Before Clicking:
Do not click on the links sent by strangers or those who are unfamiliar with you from unsolicited messages and email. Use another trusted channel to verify the authenticity of the sender [1].
Examine Message Content:
Pay attention to typographical and grammatical mistakes as professional associations follow the strict rules concerning the mode of communication. These phishing messages usually feature some minor errors.
Verify Website URLs:
Ensure you confirm the site’s URL before entering your details. Legitimate websites typically use secure connections (https: They should be registered and have recognizable domain names.
Use Security Software:
Download legitimate mobile security software containing anti-phishing mechanisms. These can also be used in real-time to detect and deny any phishing attacks.
Keep Software Updated:
Ensure that you regularly upgrade the OS of your phone as well as the applications whose vulnerabilities could be exploited by the attackers.
Conclusion:
There is a large concern on mobile phishing that compromises the confidentiality in this highly interconnected society nowadays. Mobile users should be wary of cybercriminals using deceptive tactics like fraudulent emails, texts, or even malicious mobila applications. Users can secure themselves by using proactive techniques such as scrutinising sender information, verification of URLS and utilization of security tools. Furthermore, there needs to be education whereby potential users are informed of dangers and trained on how to tell apart genuine messages from phishing attempts. Thus, regular updates, app stores, and two-factor authentication are crucial in maintaining robust protection as we travel online. Eventually, through knowledge, vigilance and preventive measures, mobile users will be able to manage this kind of phishing and avoid breaches into their confidential data within a complex mobile environment.
References:
- Goel, D., & Jain, A. K. (2018). Mobile phishing attacks and defence mechanisms: State of art and open research challenges. computers & security, 73, 519-544.
- Felt, A. P., & Wagner, D. (2011). Phishing on mobile devices.
- Shahriar, H., Klintic, T., & Clincy, V. (2015). Mobile phishing attacks and mitigation techniques. Journal of Information Security, 6(03), 206.
- Amro, B. (2018). Phishing techniques in mobile devices. arXiv preprint arXiv:1802.04501.
- Mishra, S., & Soni, D. (2019, August). SMS phishing and mitigation approaches. In 2019 twelfth international conference on contemporary computing (ic3) (pp. 1-5). IEEE.
- Almomani, A., Gupta, B. B., Atawneh, S., Meulenberg, A., & Almomani, E. (2013). A survey of phishing email filtering techniques. IEEE communications surveys & tutorials, 15(4), 2070-2090.
- Foozy, C. F. M., Ahmad, R., & Abdollah, M. F. (2013). Phishing detection taxonomy for mobile device. International Journal of Computer Science Issues (IJCSI), 10(1), 338-344.
- Poonia, V., Goyal, M. K., Gupta, B. B., Gupta, A. K., Jha, S., & Das, J. (2021). Drought occurrence in different river basins of India and blockchain technology based framework for disaster management. Journal of Cleaner Production, 312, 127737.
- Gupta, B. B., & Sheng, Q. Z. (Eds.). (2019). Machine learning for computer and cyber security: principle, algorithms, and practices. CRC Press.
- Singh, A., & Gupta, B. B. (2022). Distributed denial-of-service (DDoS) attacks and defense mechanisms in various web-enabled computing platforms: issues, challenges, and future research directions. International Journal on Semantic Web and Information Systems (IJSWIS), 18(1), 1-43.
- Almomani, A., Alauthman, M., Shatnawi, M. T., Alweshah, M., Alrosan, A., Alomoush, W., & Gupta, B. B. (2022). Phishing website detection with semantic features based on machine learning classifiers: a comparative study. International Journal on Semantic Web and Information Systems (IJSWIS), 18(1), 1-24.
Cite As
REDDY K.T (2023) Unmasking Mobile Phishing Strategies, Tactics, and Defence, Insights2Techinfo, pp.1