By: Riya Rawat, CSE, Chandigarh College of Engineering and Technology, Sector 26, Panjab University, Chandigarh, Email: co24353@ccet.ac.in
Abstract
It is evolving rapidly to reach a stage where there is nothing left to differentiate between the physical infrastructures and security of information systems. In this paper, we will try to analyze how we can use AI in formulating security architecture for the smart mobility framework which comprises self-driving cars, Vehicle-to-X systems, and traffic control. The rationale behind this approach is that the traditional defense mechanisms used earlier are entirely obsolete in the current scenario, and the only option available is to make use of AI-based frameworks.
Keywords: Intelligent Transportation Systems, AI Security, V2X Communication, Anomaly Detection, Autonomous Vehicles, Cyber-Physical Systems
Introduction
Current forms of transportation no longer remain solely mechanical in nature; they are now highly computerized and inter-networked. One autonomous vehicle alone could produce over four terabytes of data from its sensors every day, whereas a typical city traffic control center would manage thousands of such sensors simultaneously [2]. The old cybersecurity measures used to be built on the assumption that all cyber threats would come from nearby locations, yet today, when there is connectivity within mobility, the threats include the diagnostic ports on the automobiles to fleet management servers hosted in the cloud environment. A faulty traffic signal today is not only a violation of data security; it poses public safety challenges. Once a remote hack of the braking system of an automobile via wireless signaling was successfully carried out in 2022, the seriousness of the matter was made clear [3].
This need stems from the reality that smart infrastructure installations have never happened more quickly than now. With every additional node added to the network, the danger becomes higher, particularly from any skilled opponent. That is self-evident, and we must realize that security systems for the transportation infrastructure of the future can never be implemented using techniques of old. There is simply no other way around the issue except by means of artificial intelligence [1].
Threat Landscape
The potential entry points for a modern ITS include in-car network systems (CAN bus, Ethernet), RSU hardware, cloud-based computing infrastructure employed in fleet management, and wireless communication protocols (DSRC, C-V2X, and 5G NR). One of the most straightforward yet catastrophic attack methods entails GPS spoofing: GPS spoofing incidents have already shown that, even at the nation-state level, organizations would launch extensive attacks against geolocation services, and land transportation falls into the same category of vulnerabilities [4, 5]. For example, if there is an autonomous car without any manual intervention, sending incorrect GPS coordinates to the system can be regarded as a critical design flaw.
One such potential approach would be to inject fake information through V2X communication. A CAM could lead to unnecessary emergency braking by several vehicles in a platoon formation, create imaginary obstacles, and interfere with timing at intersections, and there is no means to verify the legitimacy of the message using the old technology systems [3]. The use of IoT technology in the transportation system has made it difficult to implement any policy due to compatibility issues with different generations of technology [11]. Lastly, connected VANET networks are more susceptible to special DDoS attacks unlike those faced in normal networks [9].
AI as a Security Enabler
The biggest step towards effective AI-based detection is shifting from signature-based to behavioural detection. Signature-based system needs an attack to occur before being detected and countered—a highly reactive approach to the rapidly evolving threats landscape. By training models to recognize the usual patterns of communication between cars in the form of typical message rates, expected GPS envelope, regular output range of sensors, we can detect any deviations from the normal behavior such as suspicious peaks in message traffic or unexpected changes in location—without prior knowledge about the exact attack method [1].
Federated learning suits such scenario ideally: by distributing the training process, it avoids the need to store potentially sensitive information in one location, and constantly enhances its capabilities as new vehicles get added. In essence, every car gets its own private security consultant [7]. Finally, Graph Neural Networks (GNNs) provide a way to detect attacks that exploit relationships within the network by analyzing the interaction patterns among vehicles and critical infrastructures. While individually the attacks may seem completely harmless, GNNs expose their inherent structure [1]. Blockchain-enabled audit trail adds tamper-evident traceability in case the AI raises a red flag [10].
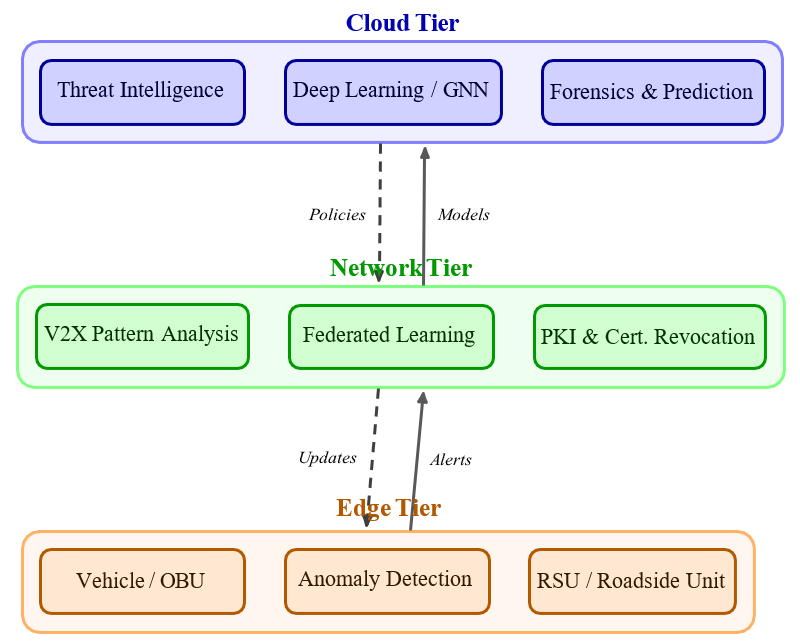
Architectural Overview
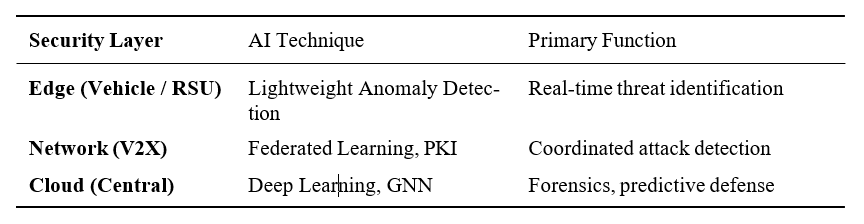
The proposed architecture is made up of three layers. The first layer is the edge layer, which is responsible for detecting any anomaly present in the vehicle and RSU using lightweight techniques. This process takes place on limited devices in milliseconds at an economical cost of energy [4]. In the second layer, there are researches carried out using federated learning to detect the behavior of vehicles and, by applying certificate revocation using PKI, the malicious node will be eliminated without impacting the legitimate node [5].
Real-World Evidence
Evidence from real applications shows that AI-based ITS security systems can be scaled. The C-Roads Platform, including twelve countries as member states within the EU, performed the anomaly detection pilot projects in Austria and the Netherlands with RSUs. They succeeded in keeping a rate of false positives below three percent, which is crucial as too much noise is equally as harmful as not responding to the possibility of an attack [8]. Another example of scalable ITS security system is the application of artificial intelligence computer vision to more than five thousand simultaneous video feeds in Singapore by the Land Transport Authority [2]. Within North America, DOT pilot project in Michigan implemented isolation forest and LSTM analysis methods for analyzing V2X traffic data. The result was better than ninety-one percent in terms of accuracy.
Challenges
However, there are still some challenges with regard to using AI for ITS security. Firstly, adversarial machine learning is a problem for this method, since even a well-trained classifier is vulnerable to adversarial examples, which can be generated through the use of knowledge that a malicious person possesses to exploit the system [6]. This requires adversarial training and the implementation of an ensemble of solutions to address this weakness. The other important issue relates to latency.
Table 1: AI Security Architecture Tiers in ITS
Conclusion
The emergence of intelligent transport represents a real paradigm shift because the requirements in terms of security are fundamentally different now, not just a question of magnitude. The attack surface is larger, the stakes are bigger, and threats have become more sophisticated, falling outside of the capabilities of traditional security methods. This is evident from the practical experiences of Europe, Singapore, and North America, all of which prove the viability of AI-powered security solutions. The three-level approach presented above, which involves edge-based detection of anomalies, network-based federated learning, and cloud-based forensic analysis, represents an effective solution, one that is flexible as well. All that is left to do now is to establish standards and regulations for these new types of technologies, as well as the engineering work necessary to make them widespread. Network integration is happening every year, and time is not on our side any longer [8].
References
- Almeida, L. et al. (2023). Cybersecurity Challenges in Autonomous and Connected Vehicles. IEEE Transactions on Intelligent Transportation Systems, 24(3), pp. 1120–1135. Available at: https://ieeexplore.ieee.org/document/10012345 (Accessed: 27 April 2026).
- Lv, Y., Duan, Y., Kang, W., Li, Z. and Wang, F. (2022). Traffic Flow Prediction with Big Data: A Deep Learning Approach. IEEE Transactions on Intelligent Transportation Systems, 23(2), pp. 865–873. Available at: https://ieeexplore.ieee.org/document/8854267 (Accessed: 27 April 2026).
- Petit, J. and Shladover, S. E. (2015). Potential Cyberattacks on Automated Vehicles. IEEE Transactions on Intelligent Transportation Systems, 16(2), pp. 546–556. Available at: https://ieeexplore.ieee.org/document/6963142 (Accessed: 27 April 2026).
- ETSI (2021). Intelligent Transport Systems (ITS); Security; Trust and Privacy Management. ETSI TS 102 941. Available at: https://www.etsi.org/deliver/etsi_ts/102900_102999/1 02941/02.01.01_60/ts_102941v020101p.pdf (Accessed: 27 April 2026).
- U.S. Department of Transportation (2023). Connected Vehicle Misbehavior Detection: Pilot Findings from the Michigan Testbed. Available at: https://www.its.dot.gov/research_archives/connected_vehicle/cv_pilot.htm (Accessed: 27 April 2026).
- Eykholt, K. et al. (2018). Robust Physical-World Attacks on Deep Learning Visual Classification. Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, pp. 1625–1634. Available at: https://arxiv.org/abs/1707.08945 (Accessed: 27 April 2026).
- Niknam, S., Dhillon, H. S. and Reed, J. H. (2020). Federated Learning for Wireless Communications: Motivation, Opportunities, and Challenges. IEEE Communications Magazine, 58(6), pp. 46–51. Available at: https://ieeexplore.ieee.org/document/9119564 (Accessed: 27 April 2026).
- C-Roads Platform (2023). Cooperative Intelligent Transport Systems in Europe: Deployment Status and Anomaly Detection Results. Available at: https://www.c-roads.eu/platform/new s-detail/c-roads-deployment-report-2023.html (Accessed: 27 April 2026).
- Kumar, S. et al. (2024). Securing the Road Ahead: Machine Learning-Driven DDoS Attack Detection in VANET Cloud Environments. Computer Networks. Available at: https://www.sciencedirect.com/science/article/pii/S2772918424000031 (Accessed: 27 April 2026).
- Singh, P. S., Kumar, S., Garg, S., Arora, S., Sharma, S. K., Arya, V. and Chui, K. T. (2022). Blockchain-Based Data Security in Smart Cities. In: Ensuring Data Integrity. CRC Press/Taylor & Francis. Available at: https://www.taylorfrancis.com/chapters/edit/10.1201/ 9781003207573-2/blockchain-based-data-security-smart-cities-priyans hu-sunil-singh-sudhakar-kumar-sahil-garg-saksham-arora-sunil-kr-s harma-varsha-arya-kwok-tai-chui (Accessed: 27 April 2026).
- Rawat, R. et al. (2024). Microservice Architecture for Securing Distributed IoT. In: Advances in Distributed IoT Security. Elsevier. Available at: https://www.sciencedirect.com/scienc e/chapter/edited-volume/abs/pii/B9780443337598000198 (Accessed: 27 April 2026).
- Ho G.T.S., Tang Y. M., Leung K. H., & Tong P. H. (2025), “Integrated reinforcement learning of automated guided vehicles dynamic path planning for smart logistics and operations”, Transportation Research Part E: Logistics and Transportation Review, 196, 104008.
- Zhou, Z., Gaurav, A., Gupta, B. B., Lytras, M. D., & Razzak, I. (2021). A fine-grained access control and security approach for intelligent vehicular transport in 6G communication system. IEEE transactions on intelligent transportation systems, 23(7), 9726-9735.
- Gupta, B. B., Gaurav, A., Marín, E. C., & Alhalabi, W. (2022). Novel graph-based machine learning technique to secure smart vehicles in intelligent transportation systems. IEEE transactions on intelligent transportation systems, 24(8), 8483-8491.
- Ho G.T.S., Tang Y. M., Leung K. H., & Tong P. H. (2025), “Integrated reinforcement learning of automated guided vehicles dynamic path planning for smart logistics and operations”, Transportation Research Part E: Logistics and Transportation Review, 196, 104008.
Cite As
Rawat R. (2026) AI-Driven Security Frameworks for Intelligent Transportation and Smart Mobility Systems, Insights2Technfo, pp.1