By: Himanshu Tiwari, International Center for AI and Cyber Security Research and Innovations (CCRI), Asia University, Taiwan, nomails1337@gmail.com
Containerization has become a pillar of modern software deployment because to its scalability and portability advantages. Nevertheless, securing the security of containerized systems is a challenging endeavor. Serious security breaches can result from vulnerabilities in container images and their dependencies. This article examines the usage of Trivy, an open-source vulnerability scanner, as a crucial instrument for boosting container security via automated vulnerability assessment and repair.
This article examines the integration of Trivy into continuous integration/continuous deployment (CI/CD) pipelines and container orchestration technologies like Kubernetes. It evaluates Trivy’s ability to detect known vulnerabilities within container images and their associated packages and libraries. The article also examines ways for ranking vulnerabilities according to their severity and possible impact.
In addition, the article investigates automated repair techniques, such as the deployment of security policies and the use of Trivy’s findings to trigger vulnerability mitigation activities. The objective is to get a thorough understanding of how Trivy, in conjunction with other security measures, may enhance container security and guard against emerging threats.
Introduction:
Containerization[1] is a technology and methodology used in computing and software development that entails packaging an application and its dependencies, such as libraries, configurations, and runtime environments, into a single, isolated unit known as a “container.” These containers are designed to be highly portable and may be performed reliably across a variety of computing environments, from a developer’s laptop to a production server or a cloud infrastructure.
Here are the key components and concepts associated with containerization:
- A container image is a lightweight, standalone, executable package that contains application code, runtime, system libraries, and configurations. It is derived from a basic image and is versionable and shareable via container registries.
- Isolation: Multiple containers can execute on the same host while being separated from one another and the underlying host system due to the process and file system isolation provided by containers. This isolation improves security and ensures that modifications to one container do not affect others.
- Portability: Containers are highly portable[2]. Once an application and its dependencies have been packed into a container image, it may be run reliably across several environments, including development, testing, and production, regardless of the underlying infrastructure.
- Efficiency: Traditional virtualization[3] is less effective than containerization. The fact that containers share the kernel of the host operating system saves resource overhead and enables containers to start quickly and utilize resources efficiently.
- Orchestration: Kubernetes[4], Docker Swarm[5], and other container orchestration[6] solutions automate the deployment, scaling, management, and networking of containers in a clustered or distributed environment. Orchestration supports containerized applications’ high availability and load balancing [7].
- DevOps and Continuous Integration/Continuous Deployment (CI/CD) [8]: Containerization is essential to contemporary DevOps processes. It enables developers to construct consistent development and production environments, integrating them seamlessly into CI/CD pipelines for automated testing and deployment.
- Docker [9]: Docker is among the most popular containerization platforms. It made containers popular by providing tools for developing, managing, and running containerized applications.
This is how Containerization works using docker:
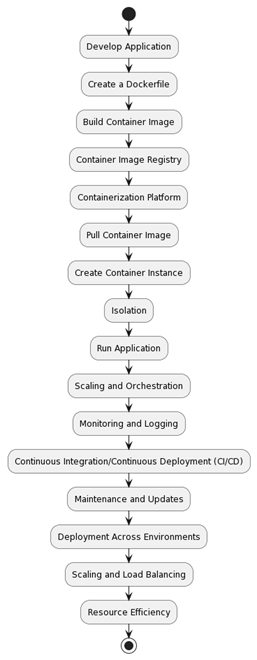
- Develop Application:
- The procedure commences with the creation of an application. This program may be a web server, a microservice, or any other deployable software.
- Create a Dockerfile:
- A Dockerfile is a text file that contains instructions for creating an application’s container image. It specifies the base image, dependency installation, and application code.
- Build Container Image:
- Using the Dockerfile, a container image is created. This is accomplished by executing the docker build command, which performs the Dockerfile instructions and generates a standalone image.
- Container Image Registry:
- The container image is typically stored in a container image registry, such as Docker Hub, Google Container Registry, or a private registry. This facilitates the image’s sharing and distribution.
- Containerization Platform:
- You deploy and manage containers using a platform for containerization. Examples of popular containerization platforms include Docker, Kubernetes, and Docker Swarm.
- Pull Container Image:
- The containerization platform retrieves the container image from the registry in order to execute an application. This maintains uniformity across all environments.
- Create Container Instance:
- The platform generates a container instance using the retrieved image. This instance contains both the application’s source code and its runtime environment.
- Isolation:
- Containers provide isolation by running each application in its own user space, separate from the host and other containers. This separation prevents conflicts and security breaches.
- Run Application:
- The application instance within the container is started. It operates with its own file system, processes, and networking setup.
- Scaling and Orchestration:
- Platforms for containerization such as Kubernetes can horizontally extend an application by producing extra container instances depending on established criteria. Orchestration tools control container lifespan, load balancing, and self-healing.
- Monitoring and Logging:
- The monitoring and logging capabilities of the platform allow you to track the health and performance of containers and apps.
- Continuous Integration/Continuous Deployment (CI/CD):
- Containerization makes CI/CD pipelines easier. Containers can be integrated into the development workflow by developers for automated testing, deployment, and rollback.
- Maintenance and Updates:
- Containers are simple to manage and update. New versions of the program can be constructed as updated container images and deployed without interruption.
- Deployment Across Environments:
- The portability of containers makes it simple to deploy the same application image in several environments, including development, testing, and production.
- Scaling and Load Balancing:
- Depending on demand, containers can be scaled up or down, ensuring optimal resource usage and high availability.
- Resource Efficiency:
- Containerization optimizes resource use by sharing the kernel of the host operating system, hence decreasing overhead in comparison to conventional virtualization.
Trivy [10] is an open-source vulnerability scanner meant to assist developers and security specialists in identifying vulnerabilities in container images and other software components. It is frequently employed in containerized settings like Docker and Kubernetes to scan container images for known security issues. Additionally, Trivy may analyze operating system packages and application dependencies for vulnerabilities.
Key features of Trivy include:
- CVE Database: Trivy maintains a comprehensive collection of known vulnerabilities utilizing the National Vulnerability Database (NVD) and other data sources. It compares the packages and components within your container images to this database in order to find any known security vulnerabilities.
- Ease of Use: Trivy has a straightforward command-line interface and supports multiple container image types. It may be integrated into existing workflows by developers and DevOps teams.
- High Speed: Trivy is renowned for its swiftness and effectiveness. It can swiftly analyze container images and offer results, making it suited for continuous integration/continuous deployment (CI/CD) environments.
- Multiple Language Support: Trivy supports numerous programming languages and ecosystems, allowing it to be used to scan a wide variety of software components, such as libraries and frameworks utilized by various applications.
- Vulnerability Assessment: Trivy gives comprehensive information about the vulnerabilities it discovers, including CVSS severity and description scores. This data assists developers in prioritizing and resolving vulnerabilities.
- Integration: Trivy may be easily connected with a variety of CI/CD technologies, container registries, and orchestration platforms such as Kubernetes, making it a powerful tool for guaranteeing the security of containerized applications throughout the development and deployment process.
Trivy helps teams find and fix vulnerabilities in their container images, hence lowering the vulnerability of containerized applications to security attacks. This helps to secure containerized applications. It is necessary to enhance the security posture of containerized environments in accordance with modern DevSecOps practices.
How Trivy works:
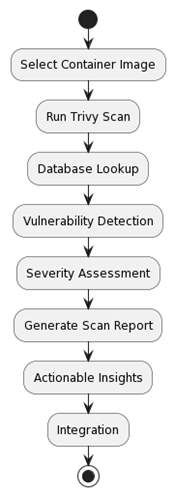
Step-by-Step Explanation of How Trivy Works:
- Select Container Image: Choose the container image you wish to check for vulnerabilities with first. This image may have been created by you or it may have come from a registry of container images.
- Run Trivy Scan: Use the chosen container picture as the input when running Trivy. To find known flaws in the image, Trivy analyzes its vulnerability database, which contains information from sources like the National Vulnerability Database (NVD).
- Database Lookup: To check the software packages and dependencies in the container image against known vulnerabilities, Trivy runs a search in its vulnerability database.
- Vulnerability Detection: Trivy uses a database lookup to identify vulnerabilities in the container image. It offers details about each vulnerability, such as the severity, description, and Common Vulnerability Scoring System (CVSS) score.
- Severity Assessment: Based on its impact and CVSS scores, Trivy evaluates each vulnerability’s severity and assigns it to one of four categories: critical, high, medium, or low.
- Generate Scan Report: Trivy creates a scan report that lists the vulnerabilities it has found, their severity, and specifics about each one.
- Actionable Insights: Examine the scan report to get insights that can be used to fix the vulnerabilities. This could entail installing patches, updating packages, or adopting other corrective measures.
- Integration: Add Trivy to your workflow for development and deployment. Trivy can be configured to automate scans at multiple points, including as during the creation of an image, in CI/CD pipelines, or in systems for container orchestration such as Kubernetes.
Conclusion:
In conjunction with other security measures, the ultimate objective of deploying Trivy is to strengthen container security and guard against potential threats. Teams may reduce the risk of security breaches and preserve the integrity of containerized applications by automating vulnerability evaluation and remediation within CI/CD pipelines and container orchestration systems such as Kubernetes.
Trivy is an essential DevSecOps solution in the age of containerized apps, enabling enterprises to remain proactive in finding and addressing vulnerabilities. By integrating Trivy as part of a comprehensive container security strategy, development and operations teams can confidently build and deploy containerized applications, knowing that security is a major focus throughout the software development lifecycle.
References
- Scheepers, Mathijs Jeroen. “Virtualization and containerization of application infrastructure: A comparison.” In 21st twente student conference on IT, vol. 21, pp. 1-7. 2014.
- Pahl, Claus. “Containerization and the paas cloud.” IEEE Cloud Computing 2.3 (2015): 24-31.
- Vaughan-Nichols, Stephen J. “New approach to virtualization is a lightweight.” Computer 39, no. 11 (2006): 12-14.
- Luksa, Marko. Kubernetes in action. Simon and Schuster, 2017.
- Marathe, N., Gandhi, A. and Shah, J.M., 2019, April. Docker swarm and kubernetes in cloud computing environment. In 2019 3rd International Conference on Trends in Electronics and Informatics (ICOEI) (pp. 179-184). IEEE.
- Khan, A., 2017. Key characteristics of a container orchestration platform to enable a modern application. IEEE cloud Computing, 4(5), pp.42-48.
- Bourke, T., 2001. Server load balancing. ” O’Reilly Media, Inc.”.
- Garg, S., Pundir, P., Rathee, G., Gupta, P.K., Garg, S. and Ahlawat, S., 2021, December. On continuous integration/continuous delivery for automated deployment of machine learning models using mlops. In 2021 IEEE fourth international conference on artificial intelligence and knowledge engineering (AIKE) (pp. 25-28). IEEE.
- Rad, Babak Bashari, Harrison John Bhatti, and Mohammad Ahmadi. “An introduction to docker and analysis of its performance.” International Journal of Computer Science and Network Security (IJCSNS) 17, no. 3 (2017): 228.
- Ram CJ, Pavithran V, Nair V. A Cumulative Tool for Docker Vulnerability Scanner. Advances in Science and Technology. 2023 Mar 27;124:748-53.
Cite As
Tiwari H. (2023) Enhancing Container Security Through Automated Vulnerability Scanning and Remediation with Trivy, Insights2Techinfo, pp.1